SOC 2 is a security framework that specifies how organizations should protect customer data from unauthorized access, security incidents, and other vulnerabilities. The American Institute of Certified Public Accountants (AICPA) developed SOC 2 around five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy.
To understand why SOC 2 is important, all you have to do is look at recent headlines. Experian, Equifax, Yahoo, LinkedIn, Facebook — high-profile data breaches are a constant in the news.
The number of data breaches in the US rose by almost 40% in Q2 2021.
Companies are facing a growing threat landscape, making information and data security a top priority. A single data breach can cost millions, not to mention the reputation hit and loss of customer trust.
There are a variety of standards and certifications that SaaS companies can achieve to prove their commitment to information security. One of the most well-regarded is the SOC report — and when it comes to customer data, the SOC 2.
What Does SOC 2 Stand for?

SOC 2 stands for Systems and Organization Controls 2.
It was created by the AICPA in 2010. SOC 2 was designed to provide auditors with guidance for evaluating the operating effectiveness of an organization’s security protocols.
The SOC 2 security framework covers how companies should handle customer data that’s stored in the cloud. At its core, the AICPA designed SOC 2 to establish trust between service providers and their customers.
What is SOC 2 Compliance?
If SOC 2 is a security framework, what does SOC 2 compliance mean? What is a SOC 2 report? What kind of organization needs a SOC 2 audit report, and when?
These are common questions for companies starting on their journey to SOC 2 compliance.
SOC 2 refers to both the security framework and the audit that checks whether a company is compliant with SOC 2 requirements.
SOC 2 defines requirements to manage and store customer data based on five Trust Services Criteria (TSC):
- Security
- Availability
- Processing integrity
- Confidentiality
- Privacy
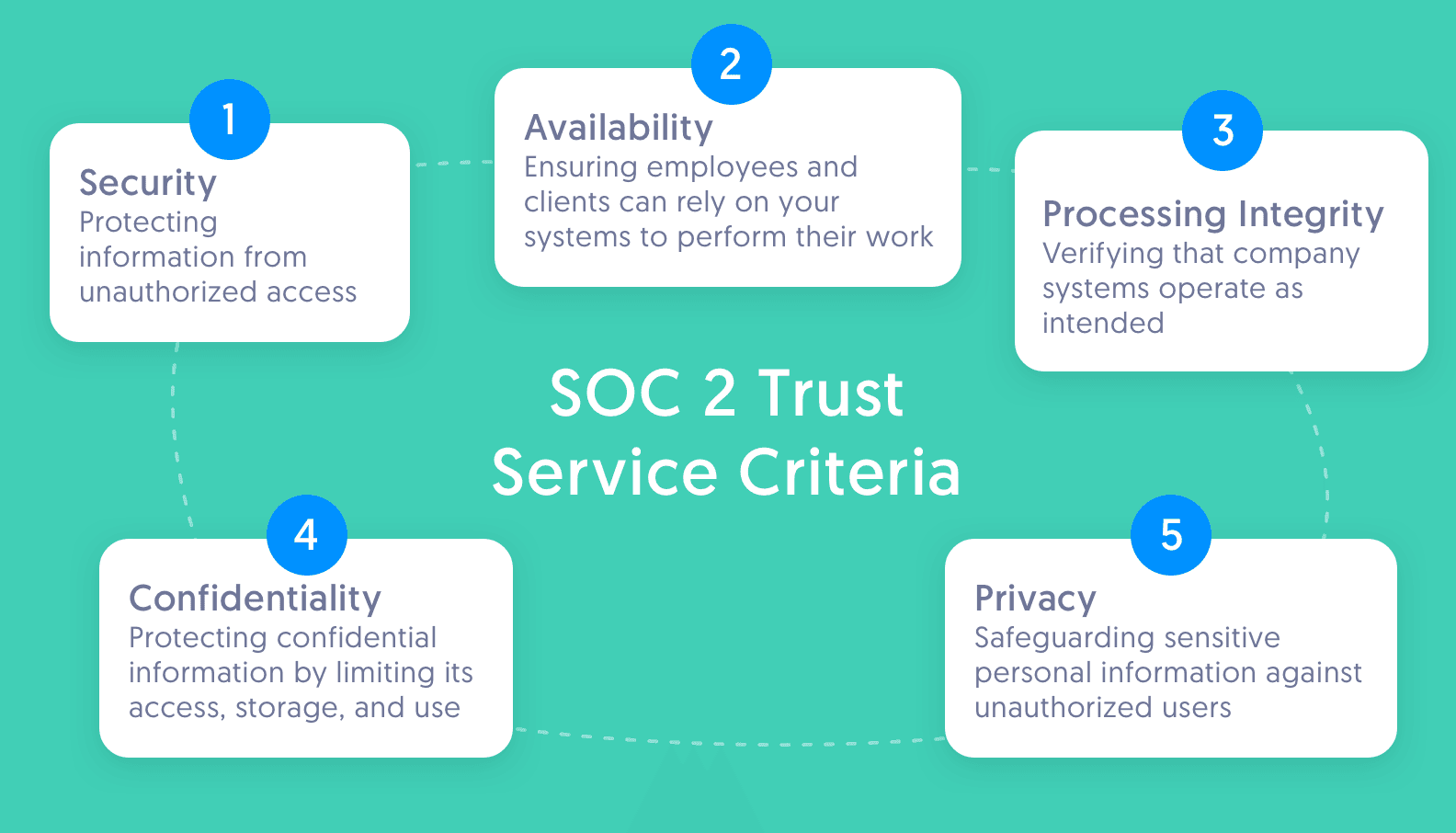
During a SOC 2 audit, an independent auditor will evaluate a company’s security posture related to one or all of these Trust Services Criteria. Each TSC has specific requirements, and a company puts internal controls in place to meet those requirements.
The Security TSC is always included in a SOC 2 audit, while the other four are optional.
Security is also referred to as the Common Criteria, since many of the security criteria are shared among all of the Trust Services Criteria.
What is a SOC 2 Audit?
While some security frameworks like ISO 27001 and PCI DSS have rigid requirements, that isn’t the case with SOC 2.
Controls and attestation reports are unique to every organization.
Each company designs its own controls to comply with its Trust Services Criteria.
An independent auditor is then brought in to verify whether the company’s controls satisfy SOC 2 requirements.
After the audit, the auditor writes a report about how well the company’s systems and processes comply with SOC 2.
Every organization that completes a SOC 2 audit receives a report, regardless of whether they passed the audit.
Here are the terms auditors use to describe the audit results:
- Unqualified: The company passed its audit.
- Qualified: The company passed, but some areas require attention.
- Adverse: The company failed its audit.
- Disclaimer of Opinion: The auditor doesn’t have enough information to make a fair conclusion.
SOC 2 Type I vs Type II: What's the Difference?
There are two types of SOC 2 reports:
- SOC 2 Type I reports evaluate a company’s controls at a single point in time. It answers the question: are the security controls designed properly?
- SOC 2 Type II reports assess how those controls function over a period of time, generally 3-12 months. It answers the question: do the security controls a company has in place function as intended?
To choose between the two, consider your goals, cost, and timeline constraints.
A Type I report can be faster to achieve, but a Type II report offers greater assurance to your customers.
We recommend going straight for the SOC 2 Type II report.
Many customers are rejecting Type I reports, and it's likely you'll need a Type II report at some point. By going straight for a Type II, you can save time and money by doing a single audit.
If you need a SOC 2 report ASAP, a Type II report that covers a shorter 3-month review period can be an ideal solution.
Who Needs a SOC 2 Report?
If you’re a service organization that stores, processes, or transmits any kind of customer data, you’ll likely need to be SOC 2 compliant.
Here’s why:
SOC 2 requirements help your company establish airtight internal security controls. This lays a foundation of security policies and processes that can help your company scale securely.
It also builds trust with your customers.
Most often, service organizations pursue a SOC 2 report because their customers are asking for it. Your clients need to know that you'll keep their sensitive data safe.
A SOC 2 report is the gold standard for providing that assurance.
A SOC 2 report can also be the key to unlocking sales and moving upmarket. It can signal to customers a level of sophistication within your organization. It also demonstrates a commitment to security. Not to mention provides a powerful differentiator against the competition.
Put simply, a SOC 2 audit is important for two reasons.
One, attaining a SOC 2 report helps your business maintain best-in-class security standards. And two, it can unlock significant growth opportunities.
The Ultimate Guide to SOC 2
Learn everything you need to know about achieving SOC 2 compliance fast.
FAQs
What does SOC 2 mean?
SOC 2 is a security and compliance standard that offers guidelines for service organizations to protect senstivie data from unauthorized access, security incidents, and other vulnerabilities. It is part of the System and Organization Controls (SOC) suite of services developed by the American Institute of Certified Public Accountants (AICPA). A SOC 2 report is often requested by customers and business partners of outsourced solution providers to provide assurance that those organizations have adequate systems and controls in place to protect critical business information.
What does a SOC 2 audit include?
A SOC 2 audit includes a rigorous examination of the design and operating effectiveness of an organization’s controls by an accredited CPA. The CPA will run tests, review evidence, and interview members of your team before producing a final report, which provides their opinion on how your service organization complies with your selected Trust Services Criteria.
Is SOC 2 mandatory?
SOC 2 is not a legal requirement like HIPAA or GDPR, but SOC 2 compliance may be required by prospects, customers, and other stakeholders looking for assurance that you have the systems and controls in place to protect their data.
Who does SOC 2 apply to?
SOC 2 applies to any service organization that stores, processes, or transmits any kind of customer data.