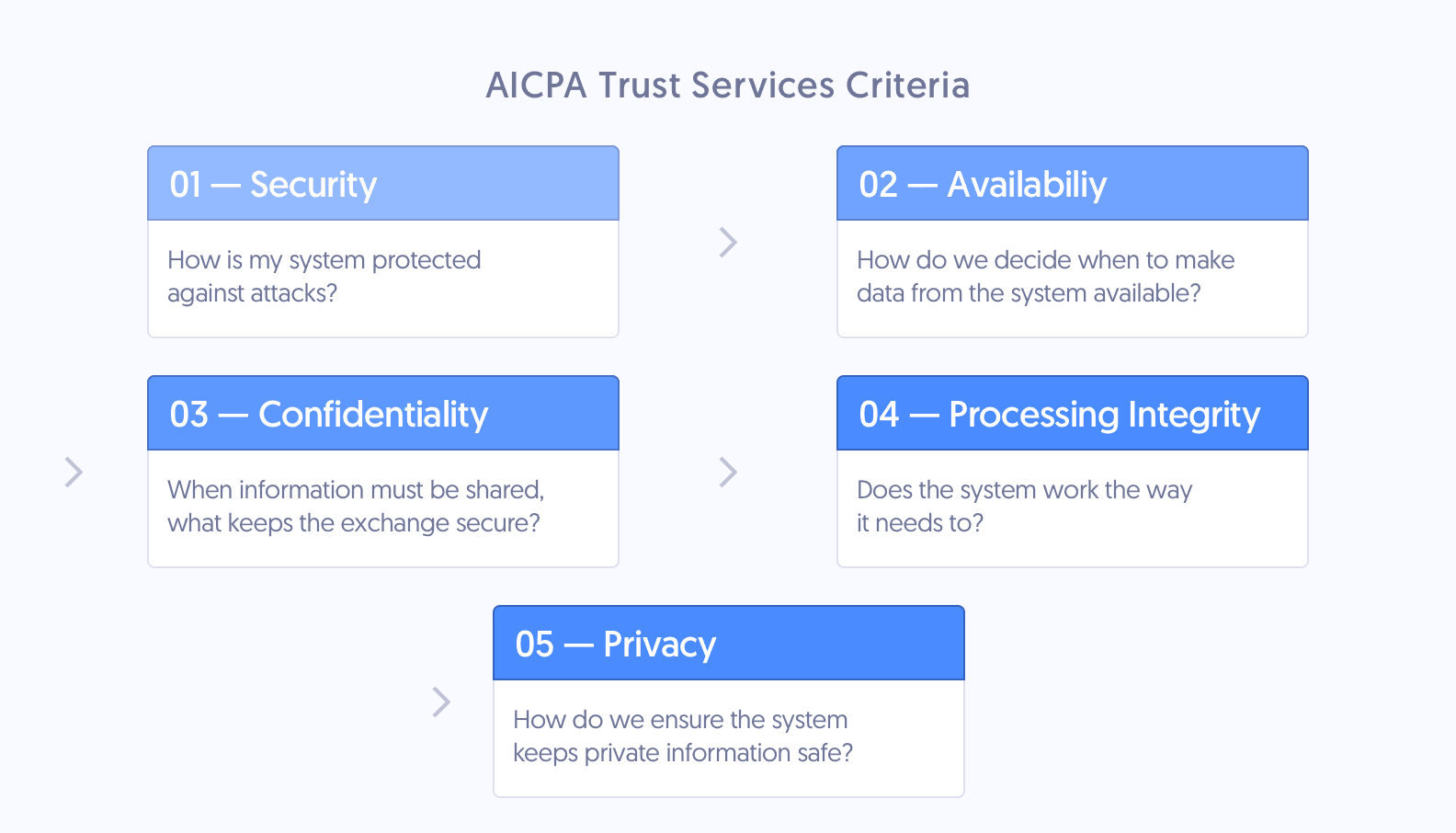
The SOC 2 framework is built on five Trust Services Criteria (formerly called the Trust Services Principles), defined by the American Institute of Certified Public Accountants (AICPA).
Get an overview of these TSC in the video below or keep reading.
These Trust Services Criteria are the basic elements of your cybersecurity posture. They include organization controls, risk assessment, risk mitigation, risk management, and change management.
The five Trust Services Criteria are:
- Security: Protecting information from vulnerabilities and unauthorized access
- Availability: Ensuring employees and clients can rely on your systems to do their work
- Processing integrity: Verifying that company systems operate as intended
- Confidentiality: Protecting confidential information by limiting its access, storage, and use
- Privacy: Safeguarding sensitive personal information against unauthorized users
Security is the only TSC required for every SOC 2 audit. Additional criteria are optional based on the services you provide to your customers.
Many organizations don’t have the resources to bring their information security systems and internal controls into compliance with every TSC.
It’s best to pursue the TSC that you’re closest to achieving or those that will have the most significant impact on your organization. You can always go for the others later.
What are the Five AICPA Trust Services Criteria?
1. Security
The Security Trust Criteria is all about protecting information from unauthorized disclosure.
The Security Criteria are also known as the Common Criteria. They prove that a service organization’s systems and control environment are protected against unauthorized access and other risks.
Security is the only Trust Services Criteria required for every SOC 2 audit. The other criteria can be added to your report scope if your organization chooses, but they are not required to achieve SOC 2 compliance.
2. Availability
The Availability Criteria determine whether your employees and clients can rely on your systems to do their work.
Some examples are data backups, disaster recovery, and business continuity planning. Each of these minimizes downtime in the event of an outage. For instance, if your data center is flooded, you have multiple power and computing redundancies. This ensures that data is available even in the event of hardware failure.
Consider adding to your SOC 2 if:
- You offer a continuous delivery or deployment platform.
- An outage would prevent your clients from building or deploying changes to their services. (E.g., cloud computing or cloud data storage providers)
3. Processing Integrity
The Processing Integrity Criteria determine whether a system works properly. Does it perform its intended functions without delay, error, omission, or accidental manipulation?
This isn’t the same as data integrity — a system can work properly with incorrect data. For example, say you’re an e-commerce company. If a customer can complete the process of placing an order, your company meets the Processing Integrity Criteria.
Now say the customer accidentally enters the wrong address. This is an example of poor data integrity. You may still meet the processing integrity requirement. Your system works the way it’s supposed to, delivering that item to the address specified. It just won’t arrive on the right customer’s doorstep.
Consider adding to your SOC 2 if:
- You provide financial reporting services, or you're an e-commerce company.
- You need to ensure your transaction processing is accurate to combat fraud.
4. Confidentiality
The Confidentiality Criteria evaluates how organizations protect confidential information. I.e., by limiting its access, storage, and use. It can help organizations define which individuals can access what data and how that data can be shared. This ensures that only authorized people can view sensitive information, like legal documents or intellectual property.
Consider adding to your SOC 2 if:
- Your organization handles confidential information. Examples include financial reports, passwords, business strategies, and intellectual property.
5. Privacy
This TSC looks at how an organization's control activities protect customers’ personally identifiable information (PII). It also ensures that a system that uses personal data complies with the AICPA’s Generally Accepted Privacy Principles.
Name, physical address, email address, and Social Security number are a few examples of information that falls under this privacy category. Data like health, race, and sexuality may be pertinent to privacy for some companies and service providers, too.
Consider adding to your SOC 2 if:
- Your organization gathers, stores, uses, preserves, reveals, or disposes of personal information.
Recommended reading

Understanding SOC 2 Compliance Requirements
Read More