SOC 2 Type 2 Compliance: Who Needs This Report & Why?
Emily Bonnie
Senior Content Marketing Manager
Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Last year, over 1.35 billion people were affected by data breaches, leakage, and exposure. According to research by PwC, mega breaches (data breaches of more than US $1M) are increasing in number, with 36% of busineeses experiencing one in 2024 compared to 27% the year before.
With this kind of risk environment, potential customers want proof that they can trust businesses to keep their sensitive data safe. One of the best ways to provide this assurance is a SOC 2 Type 2 report. But what is a SOC 2 Type 2 (or Type II) report, and how do you get one?
In this article, we’ll explain everything you need to know about SOC 2 Type 2 compliance, including how it differs from other SOC audits and reports, how it can benefit your business, and what it takes to get a SOC 2 Type 2 report.
What is the AICPA SOC 2 framework? Comparing SOC 2 vs SOC 1 vs SOC 3
In today’s cyberthreat-infested landscape, customers demand honesty and transparency in how you handle their sensitive data. They’ll want you to complete detailed security questionnaires or show proof that your organization complies with widely-recognized security frameworks such as SOC 2 and ISO 27001.
The System and Organizations Control (SOC) reports offer some of the best ways to demonstrate that you have effective information security controls in place.
The most common types of SOC reports are SOC 1, SOC 2, and SOC 3. Let's make sure we understand the difference between these types before diving into SOC 2 Type II reports specifically.

SOC 1 and SOC 2 reports are similar in that they are both assessed against the SSAE 18 auditing standard. But a SOC 1 report is for companies whose internal security controls can affect a user entity’s financial reporting, such as payroll or payment processing companies.
A SOC 2 report helps organizations prove their information security controls based on five Trust Services Criteria: security, availability, processing integrity, confidentiality, and privacy. This report assures user entities that:
- You have the required data security controls in place to protect customer data against unauthorized access
- You can detect anomalies and security incidents across the entire ecosystem
- Besides preventing risk situations, you can quickly repair damage and restore functionality in the event of a data breach or system failure
This report is ideal for any service organization that stores, processes, or transmits any kind of customer data.
SOC 3 reports are related to SOC 2 reports. Whereas SOC 2 reports are private internal documents that are typically only shared with customers and prospects under an NDA, SOC 3 reports are less detailed, general use reports that can be distributed or posted to the public.
Now that we have a better understanding of how SOC 2 relates to SOC 1 and 3, let's dive deeper into SOC 2.
Recommended reading

SOC 2 Explained: Understanding the Report Types, Requirements & Process [+ Free Resources]
What is SOC 2 Type 2 compliance?
SOC 2 Type 2 compliance means your organization has implemented a robust set of internal security controls and those controls have been independently evaluated for effectiveness over a period of time (typically 3 to 12 months) by a licensed CPA firm.
Achieving this type of compliance involves two parts. The first is implementing controls to meet the requirements of the American Institute of Certified Public Accountants (AICPA)'s Trust Services Criteria:
- Security (the only required TSC): Protecting information from vulnerabilities and unauthorized access
- Availability: Ensuring employees and clients can rely on your systems to do their work
- Processing integrity: Verifying that company systems operate as intended
- Confidentiality: Protecting confidential information by limiting its access, storage, and use
- Privacy: Safeguarding sensitive personal information against unauthorized users
The second is demonstrating the design and operating effectiveness of those controls over a period of time (rather than a point in time) through formal audit procedures.
Let's take a closer look at how SOC Type 2 differs from Type 1 below.
What is the difference between a SOC 2 Type 1 and SOC 2 Type 2 report?

There are two different types of SOC 2 reports: SOC 2 Type 1 and SOC 2 Type 2 (sometimes referred to as "SOC 2 Type I" and "SOC 2 Type II").
- The SOC 2 Type 1 report covers the suitability of design controls and the operating effectiveness of your systems at a specific point in time. It affirms that your security systems and controls are comprehensive and designed effectively. Because of this shorter audit window, a SOC 2 Type 1 report is faster and less expensive than a SOC 2 Type 2 report.
- The SOC 2 Type 2 report assesses the design and operating effectiveness of your internal controls over a period of time, typically 3-12 months. This means SOC 2 Type 2 audits require a greater investment of both time and resources, but the resulting report offers greater assurance to customers. In fact, a SOC 2 Type 2 report is often a requirement for unblocking mid-market and enterprise deals.
Since it's likely that you'll need a Type 2 report at some point, especially if trying to move upmarket, we recommend going straight for this report. You can save time and money by doing a single audit rather than a Type 1 audit first and Type 2 audit later.
For more information on the differences between SOC 2 Type 1 vs Type 2 audits, check out the video below.
To understand why a SOC 2 Type 2 (Type II) report provides stronger assurance than a Type 1 (Type I) report, let's look at what a Type 2 report covers exactly.
What does a SOC 2 Type 2 report cover?
A SOC 2 Type 2 report examines a service provider’s internal controls and systems related to the Trust Service Criteria, formerly known as the Trust Services Principles. While the scope of this report must include the security criteria, it can also include up to four other criteria (availability, processing integrity, confidentiality, and privacy of data).
The scope of a SOC 2 Type 2 report is bigger than a Type 1 report because it delves into the nitty-gritty details of your infrastructure service system throughout the specified period of time.
It focuses on the following areas:
- Infrastructure: The physical and hardware components (networks, facilities, and equipment) that support your IT environment and help you deliver services.
- Software: The operating software and programs (utilities, applications, and systems) you use to facilitate data and system processing.
- People: The personnel (managers, developers, users, and operators) involved in the management, security, governance, and operations to deliver services to customers.
- Data: The information (files, databases, transaction stream, and tables) you use or process within the service organization.
- Procedures: The manual or automated procedures that bind processes and keep service delivery ticking along.

Now that we have a better sense of what a SOC 2 Type 2 report is, let's take a closer look at why it's important.
Benefits of SOC 2 Type 2 compliance
Businesses have been moving operations from on-premise software to a cloud-based infrastructure, which boosts processing efficiency while cutting overhead expenses. However, moving to cloud services means losing tight control over the security of data and system resources.
People outside your organization will host, handle, and maintain data on your behalf. The sub-processor will have access to your sensitive information, which leaves you vulnerable to data breaches. Research by Pentera shows that more than half (51%) of enterprises reported a data breach in the past 24 months.
So why get a SOC 2 report? This report assures your customers that your security program is properly designed and operates effectively to safeguard data against threat actors.
It shows that you’re responsible with:
- Process monitoring
- Encryption control
- Intrusion detection
- User access authentication
- Disaster recovery
The extra time and money you invest in a SOC 2 Type 2 audit (sometimes written as “SOC 2 Type II audit”) can deliver incredible value to your organization. Cloud service providers like AWS and SaaS vendors are typically asked by their customers’ legal, security, and procurement departments to provide a copy of their SOC 2 report. Without one, the sales process can grind to a halt, especially when moving upmarket.
Other benefits of SOC 2 Type 2 compliance include:
- Protection against data breaches: A SOC 2 Type 2 report can also protect your brand’s reputation by establishing best practice security controls and processes and preventing a costly data breach.
- Competitive differentiation: A SOC 2 report offers potential and current customers definitive proof that you are committed to keeping their sensitive data safe. Having a report in hand provides a significant advantage to your company over competitors that don’t have one.
- Efficient internal processes: Going through a SOC 2 audit can pinpoint areas where your organization can streamline processes. It also ensures everyone within your company understands their role and responsibilities regarding data security.
Now let's look at when organizations might move beyond wanting a SOC 2 Type 2 report to needing one.
Who needs a SOC 2 Type 2 report?
Any business handling sensitive customer information might need a SOC 2 Type 2 report. It’s particularly useful for cloud computing vendors, managed IT services providers, software-as-a-service (SaaS) providers, and data centers that need to show current and potential customers that they have the appropriate safeguards in place to keep sensitive data secure.
If a service organization determines they need a SOC 2 report, when do they need a SOC 2 Type 2 (Type II) over SOC 2 Type 1 (Type I)? Generally, it comes down to what customers, prospects, partners, and investors demand.
- A SOC 2 Type 1 report demonstrates your commitment to protecting sensitive data. However, it only represents a point-in-time snapshot, which may not be sufficient for enterprise clients.
- The SOC 2 Type 2 report breaks that ceiling, allowing businesses to scale to the next level and net contracts with larger enterprises that know their databases are prime targets for cybercriminals and want to avoid costly hacking incidents.
Whether you’re trying to unblock deals with startups or enterprise clients, customers want assurance that you’ve woven security controls into your organization’s DNA. They also want to see that you have defined risk management, access controls, and change management in place, and that you monitor controls on an ongoing basis to make sure they are working optimally. A SOC 2 Type 2 report provides that assurance.
If your organization has decided to pursue a SOC 2 Type 2 report, the next step is understanding what the audit process involves, in terms of preparation and the audit itself.
Recommended reading

Do You Need a SOC 2® Report? Answers to Common SOC 2 Compliance Questions
SOC 2 Type 2 Audit Checklist
Preparing for a SOC 2 Type 2 audit requires more time, coordination, and evidence than a SOC 2 Type 1 audit. While Type 1 validates your control design at a single point in time, a Type 2 audit evaluates how effectively those controls operate over a sustained period, typically 3 to 12 months. That means you’ll need to demonstrate not just intent but follow-through.
Here are a few key steps from our SOC 2 audit checklist to help you better understand the required audit prep:
- Conduct a readiness assessment: Start with a SOC 2 self-assessment to identify any gaps in your current control environment. This step is crucial to avoid costly delays once the audit period begins.
- Define your audit scope and Trust Services Criteria (TSC): Determine which of the five TSCs apply to your organization. This decision will not only shape your audit’s complexity and timeline—it will also shape what requirements you have to meet. For example, the Security Criteria requires organizations to implement strong logical and physical access controls (or password requirements). You may need to work with your auditor, internal compliance team, or an external compliance manager.
- Map and review applicable controls: Use a comprehensive SOC 2 compliance checklist to ensure you’ve implemented the necessary controls and documented them appropriately. You’ll also need to assign ownership and demonstrate consistency throughout the audit window.
- Establish audit timelines and documentation: A Type 2 audit evaluates evidence over time, so start collecting documentation as early as possible. Outline a timeline that accounts for both the observation period and your team’s bandwidth to respond to auditor requests.
Now that we have a better sense of the audit readiness process, let's go over the steps involved in the audit itself.
SOC 2 Type 2 Audit Checklist
Check items off this interactive checklist to gauge your company’s level of SOC 2 Type 2 compliance.
What happens during a SOC 2 Type 2 audit?
A typical SOC 2 Type 2 (Type II) audit involves the following stages:
- Scoping procedures: You (the service organization) will determine applicable trust services criteria with the help of a licensed CPA firm or agency accredited by the AICPA.
- Gap analysis or readiness assessment: The auditor will pinpoint gaps in your security practices and controls. Moreover, the auditor will create a remediation plan and help you implement it.
- Attestation engagement: The auditor will set the list of deliverables as per the AICPA attestation standards (described below). They will then perform the examination to determine the suitability of design controls and operating effectiveness of systems relevant to the applicable TSC over the specified period.
- Report writing and delivery: The auditor will deliver the report covering all the areas described below.
As per AICPA requirements, only licensed CPA firms can conduct a SOC 2 audit.
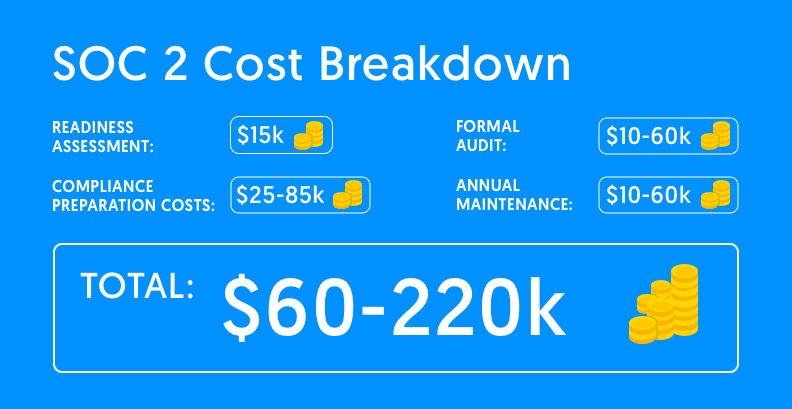
How much does a SOC 2 Type 2 audit cost?
SOC 2 Type 2 auditing costs vary between $10,000 and $60,000, on average. The cost will depend on factors such as:
- The number of applicable Trust Service Criteria
- The scope and complexity of your control environment
- The number of in-scope applications
- The number of employees and physical locations included in the audit
- The level of support needed throughout
- The SOC 2 automation tool you're using (if using no automation or a limited tool, then your costs will likely be higher)
What’s included in a SOC 2 Type 2 report?
The SOC 2 Type II report includes four main sections:
1. Management assertion
The management assertion is where organization leadership makes claims about its own systems and organization controls. The auditor measures your description of infrastructure service systems throughout the specified period against the relevant Trust Services Criteria.
2. Independent auditor's report
In this section, the auditor provides a summary of their examinations per AICPA’s attestation standards.
The auditor will deliver their opinion on whether:
- The management assertion is fairly presented as per the description criteria
- The internal controls were suitably designed and worked effectively to meet applicable TSPs throughout the specified period
3. System description
The SOC 2 system description offers a detailed overview of the services you provide and the systems under audit, including people, processes, data, software, and infrastructure.
It also describes relevant aspects of the internal control environment, monitoring, information and communication, and risk assessment processes.
4. Control tests for applicable Trust Services Criteria
Here you’ll find a description of every test the auditor performed over the course of the audit, including test results, for the applicable TSC.
You might be wondering why these four sections?
How AICPA guidelines shape the structure of your report
The AICPA is responsible for developing and maintaining a set of guidelines for the contents of a SOC 2 report. These guidelines are found in several important documents, including:
- The TSP 100 includes points of focus, which serve as implementation guidance for each of the five Trust Services criteria.
- The DC Section 200 includes description criteria or guidelines for how to write the biggest section of the SOC 2 report: the description of the service organization’s system.
In 2022 and 2023, the AICPA updated its attestation standards with revised criteria (TSP Section 100) and description criteria (DC Section 200).
These updates impact how service organizations describe their systems and how controls are tested, making it even more important to work with an experienced auditor and to leverage a SOC automation platform like Secureframe. Our compliance experts continually consider updates like these when building out tests in the Secureframe platform, and where needed, highlight suggested changes. That means you don’t have to sift through the TSP 100 Revised Points of Focus on your own to determine what they mean for you and your organization's control environment.
Because SOC 2 Type 2 reports cover a specific time period, it’s important to keep your report current with annual audits to maintain trust and prove your controls are still operating effectively. Automation can also help you maintain compliance and reduce the costs, efforts, and complexity of preparing for a SOC 2 Type II audit every year.
SOC 2 Type 2 Report Example
Download our illustrative example of a SOC 2 Type 2 Report to get a sense of what a report might include, how it might be organized, and how long it may be. This can help you if you're preparing for an audit or determining if a SOC 2 Type 2 report is the right choice for your organization.
How long is a SOC 2 Type 2 report valid?
The SOC 2 (Type 1 or Type 2) report is valid for one year following the date the report was issued. Any report that’s older than one year becomes “stale” and is of limited value to potential customers.
As a result, the golden rule is to schedule a SOC audit every 12 months.
However, the annual audit rule isn’t written in stone. You can undertake the audit as often as you make significant changes that impact the control environment. For example, if your service organization is facing ongoing concerns about cybersecurity controls, you can undergo SOC 2 Type 2 audits bi-annually.
Keep in mind your customers are watching how frequently you schedule SOC 2 reports. Any irregular scheduling could signal a lack of commitment to SOC 2 compliance.
A faster, easier path to SOC 2 Type II compliance
Getting a SOC 2 Type II audit report can be expensive, time-consuming, and overwhelming. Beyond the capital investments, the auditing process can take precious time away from your employees, impacting overall productivity.
Secureframe’s compliance automation platform streamlines the entire process, helping you get audit-ready in weeks, not months:
- Save time on policy creation with our library of auditor-approved policy templates
- Automatically collect evidence and share with your auditor in a secure Data Room
- Continuously monitor your tech stack and get alerts for threats and non-conformities to easily maintain compliance year after year
- Achieve compliance across multiple frameworks, including ISO 27001, PCI DSS, HIPAA and over a dozen more
- Get expert, end-to-end support from compliance experts and former auditors throughout the entire process
Learn more about how our platform can help you achieve SOC 2 Type 2 compliance, or schedule a demo today.
Use trust to accelerate growth
FAQs
What is SOC 2 Type II vs SOC 2 Type II?
A SOC 2 Type I report is like a snapshot – it looks at your security controls at a specific moment in time. SOC 2 Type II reports examine how your controls perform over a period of time, usually 3-12 months. Type II reports are more thorough than Type I reports and generally more requested by customers, prospects, and partners.
Why does this blog use both “SOC 2 Type 2” and “SOC 2 Type II”?
While “SOC 2 Type 2” is the preferred term by the AICPA, you may still see it referred to as “SOC 2 Type II.”
“SOC 2 Type 2” is the preferred terminology according to the AICPA, the governing body that created the framework. However, you may still see “SOC 2 Type II” used in audit reports and across the web. The use of Roman numerals is a legacy convention that remains common in legal documents and other formal contexts, and many people continue to search using this version.
To make this guide accessible and useful to the broadest audience, we include both variations throughout the blog.
What is SOC 2 Type 2 vs SOC 3?
SSAE 18 includes three types of reports that review different aspects of a company's operations: SOC 1, SOC 2, and SOC 3. A SOC 2 report is very detailed and intended for people who need to understand all the technicalities of a company's internal controls, like auditors and IT personnel. On the other hand, a SOC 3 report is a summary version of the SOC 2 report that's meant for the general public.
How to implement SOC 2 Type 2?
The SOC 2 compliance process involves several steps, including an external audit. First, organizations must decide the scope of their SOC 2: whether to pursue a SOC 2 Type 1 or Type 2 report, and which Trust Services Criteria to include. Next they conduct a gap analysis to identify and implement any missing controls. After completing a readiness assessment, they select an auditor and begin the formal audit process. At the end of the audit, the auditor will issue the final report.
What is SOC 1 vs SOC 2 vs SOC 3?
SOC 1 assesses internal controls for financial reporting. SOC 2 reports evaluate internal controls for the security, confidentiality, processing integrity, and availability of customer data. SOC 3 reports examine the same controls as a SOC 2 report, but are less specific and tailored for a general audience.
What’s the difference between an ISO 27001 certification and a SOC 2 Type 2 report?
ISO/IEC 27001 certification is issued by an accreditation body after an organization undergoes an audit that shows their information security management system (ISMS) meets ISO 27001's rigorous requirements. SOC 2 Type 2, in contrast, is an attestation report issued by a CPA firm that verifies an organizations' controls are designed and operating effectively over a period to meet relevant AICPA Trust Services Criteria. While both provide third-party assurance that the organization can protect customer data, SOC 2 is often more recognized in North America and commonly requested by U.S.-based enterprise buyers.
Dive deeper into the differences between ISO 27001 and SOC 2 here.
What is the difference between PCI DSS and SOC 2 Type 2?
Both standards help organizations protect sensitive data. However, the purpose is slightly different. The Payment Card Industry Data Security Standard (PCI DSS) is designed to protect cardholder data, with specific requirements for data encryption and access controls. PCI compliance involves either a report on compliance (RoC) conducted by a qualified security assessor, or a self-assessment questionnaire (SAQ). SOC 2 covers a broader range of sensitive data, with various controls to safeguard data security, availability, privacy, and processing integrity. SOC 2 compliance involves an external audit conducted by a certified public accountant (CPA).

Emily Bonnie
Senior Content Marketing Manager
Emily Bonnie is a seasoned digital marketing strategist with over ten years of experience creating content that attracts, engages, and converts for leading SaaS companies. At Secureframe, she helps demystify complex governance, risk, and compliance (GRC) topics, turning technical frameworks and regulations into accessible, actionable guidance. Her work aims to empower organizations of all sizes to strengthen their security posture, streamline compliance, and build lasting trust with customers.

Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Rob Gutierrez is an information security leader with nearly a decade of experience in GRC, IT audit, cybersecurity, FedRAMP, cloud, and supply chain assessments. As a former auditor and security consultant, Rob performed and managed CMMC, FedRAMP, FISMA, and other security and regulatory audits. At Secureframe, he’s helped hundreds of customers achieve compliance with federal and commercial frameworks, including NIST 800-171, NIST 800-53, FedRAMP, CMMC, SOC 2, and ISO 27001.