The SOC 2® framework includes 5 Trust Services Criteria made up of 64 individual requirements. Controls are the security measures you put into place to satisfy these requirements. During your audit, the CPA will evaluate your controls to create your attestation/audit report.
Internal controls can be policies, procedures, rules, and mechanisms to ensure compliance.
An example would be requiring one person to approve an invoice before another person pays it.
So how many controls are there in SOC 2? As many as your organization needs to be compliant with your selected TSC. Check out this video below to hear some important ones your organization should have in place.
AICPA SOC 2 Points of Focus
Unlike other information security frameworks like ISO 27001, there is no universal SOC 2 requirements checklist.
In its official SOC 2 guide, the American Institute of Certified Public Accountants (AICPA) does provide "points of focus" for each Trust Services Criteria (formerly Trust Services Principles). These points of focus are examples of how an organization can satisfy requirements for each criterion. They're intended to help organizations and service providers design and implement their control environment.
It’s important to note that the points of focus are not requirements. They're guidelines to help you better understand what you can do to meet each requirement. They’re also a good resource for understanding how an auditor will think about each TSC when evaluating and testing your organization's controls.
Here’s an example from the AICPA SOC 2 guide showing points of focus for CC1.1: Demonstrating a commitment to integrity and ethical values.
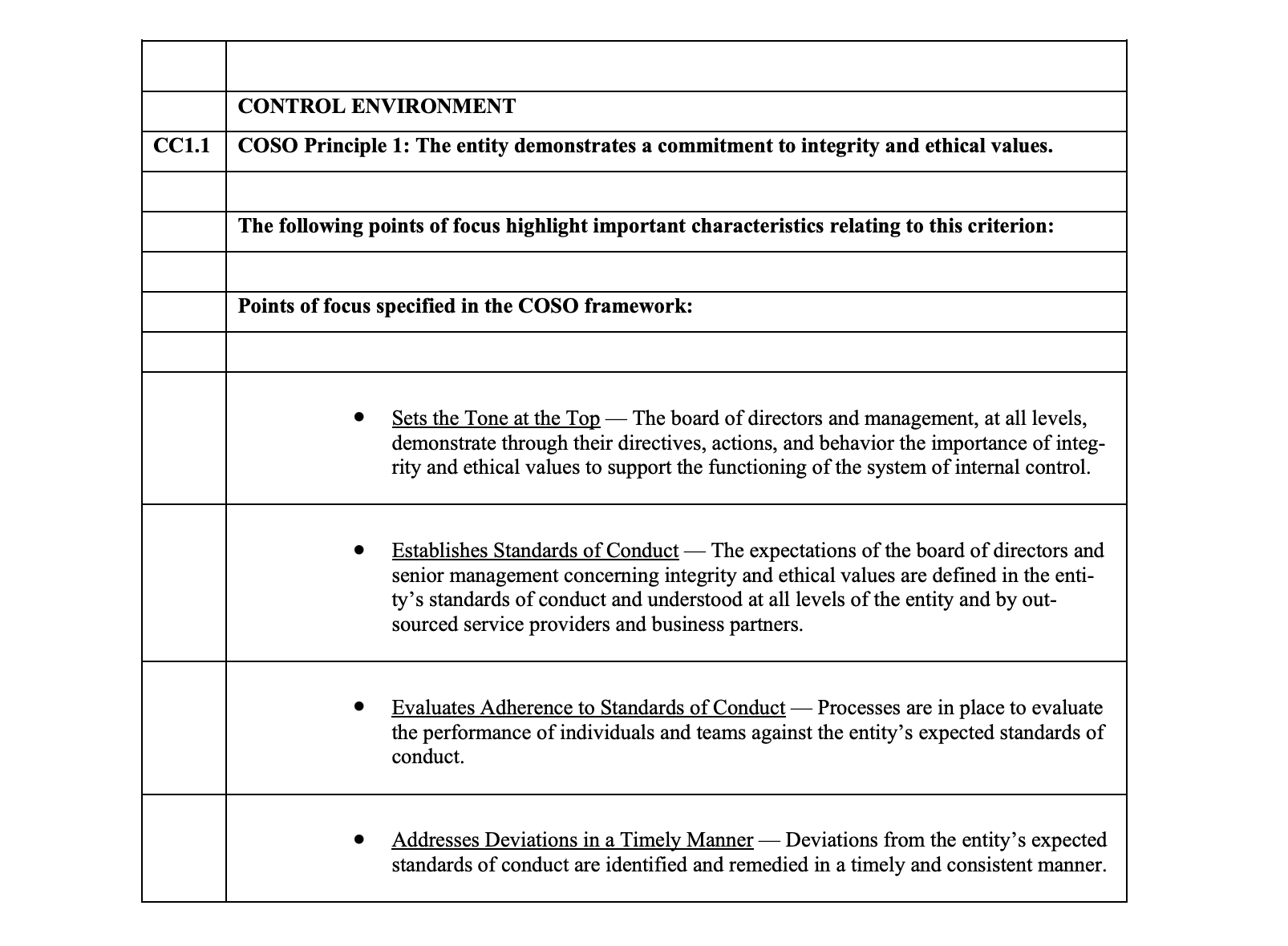
The second point of focus listed discusses standards of conduct that are clearly defined and communicated across all levels of the business. Implementing a Code of Conduct policy is one example of how organizations can satisfy CC1.1’s requirements.
So while there are specific criteria required for compliance, how your organization satisfies them is up to you and your CPA auditor. Ultimately, no two SOC 2 audits are identical.
Let’s explore what each Trust Services Criteria means and what service organization controls an auditor might look for based on each.
SOC 2 Controls List

Security Controls
Security is the fundamental core of SOC 2 compliance requirements. The category covers strong operational processes around security and compliance. It also includes defenses against all forms of attack, from man-in-the-middle attacks to malicious individuals physically accessing your servers.
An auditor might check for two-factor authentication systems and web firewalls. They’ll also look at things that indirectly affect cybersecurity and data security, like policies determining who gets hired for security roles.
Privacy Controls
Privacy applies to any information that’s considered sensitive. To meet the SOC 2 requirements for privacy, an organization must communicate its policies to anybody whose customer data they store.
If the organization collects any sensitive information, it must:
- Obtain consent from the subject
- Limit the amount of private information it collects
- Gather it by lawful means
- Use it only for the purposes it was collected for
Finally, when the personal information has served its purpose, the service organization is required to dispose of it.
Confidentiality Controls
Confidential information is different from private information in that, to be useful, it must be shared with other parties. The most common example is health data. It’s highly sensitive, but it’s worthless if you can’t share it between hospitals, pharmacies, and specialists.
Instead of keeping the information totally secure, the confidentiality category focuses on making sure it's shared securely.
Meeting the SOC 2 confidentiality criteria requires a clear process for identifying confidential information. Confidential data must be protected against unauthorized access until the end of a predetermined retention period of time, then destroyed.
Processing Integrity Controls
Do the systems used to store, process, and retrieve information work the way they’re supposed to?
Some controls in the PI series refer to the organization’s ability to define what data it needs to achieve its goals. Others define processing integrity in terms of inputs and outputs. For example, if a customer inputs an order on an e-commerce website, the output is prompt delivery of the product.
Outputs should only be distributed to their intended recipients. Any errors should be detected and corrected as quickly as possible.
Availability Controls
The Availability controls in SOC 2 focus on minimizing downtime. They are especially important for SaaS and cloud computing providers.
Are the systems of the service organization backed up securely? Is there a recovery plan in case of a disaster? Is there a business continuity plan that can be applied to any unforeseen event or security incident? A formal risk assessment, risk management, and risk mitigation process is important for identifying threats to data centers and maintaining availability.
A1 series controls ask organizations to:
- Predict system capacity
- Identify and mitigate environmental threats
- Identify what data to back up
SOC 2 Evidence Collection Spreadsheet
The average SOC 2 has over 200 security requirements to implement. Be fully prepared for your audit by collecting and organizing the evidence you’ll need.
FAQs
How many SOC 2 controls are there?
The SOC 2 framework includes 5 Trust Services Criteria made up of 64 individual requirements. Controls are the security measures you put into place to satisfy SOC 2 requirements. The number of controls you put in place depends on the number of TSC you include in your audit and the complexity of your infrastructure and organization. Typically, a SOC 2 Type 2 audit that covers security (the only required TSC) will address the suitability of the design and operating effectiveness of 80 controls on average. For service organizations that are all in the cloud, the average drops to 60. For organizations with more complex infrastructure and organizational structure, then the average goes up to 100.
What is the difference between SOC 1 and SOC 2 controls?
SOC 2 controls are controls put in place at a service organization that are relevant to security, availability, processing integrity, confidentiality, or privacy. SOC 1 controls are controls put in place at a service organization that are relevant to user entities’ (e.g. entities that use service organizations) internal control over financial reporting.
What's an example of a SOC 2 control?
An example of a SOC 2 control is having an information security policy reviewed by the Chief Technology Officer to ensure it includes strategic plan considerations, applicable laws for the respective territories, and roles and responsibilities for leadership and officers.