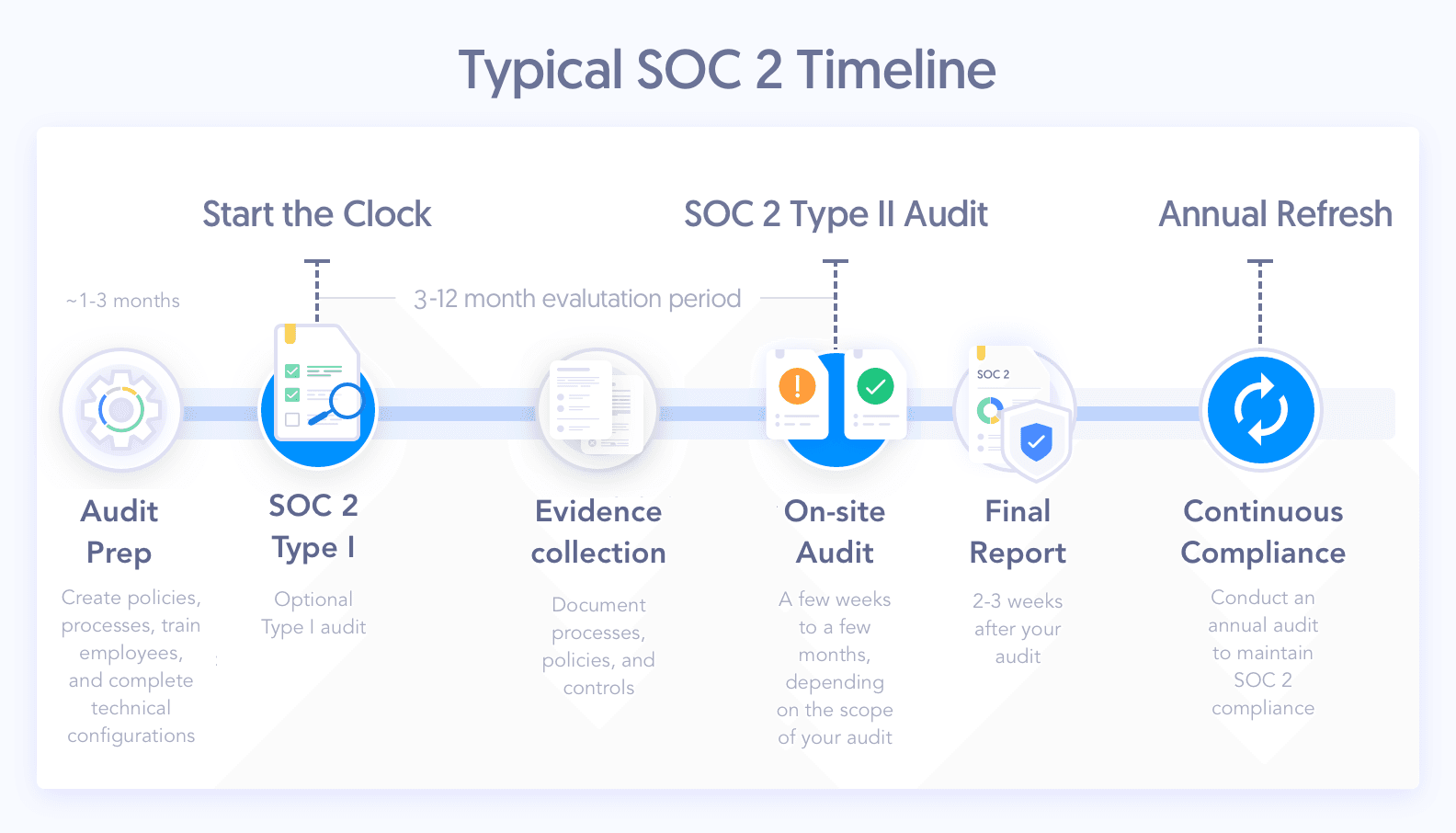
The traditional process of getting a SOC 2 report can be pretty lengthy and involved. Especially if you opt for a SOC 2 Type II report.
Compliance automation software can slash this timeline from months to weeks. By automatically monitoring your infrastructure and collecting evidence, it cuts audit preparation from months to weeks.
Regardless of which approach you choose, SOC 2 has three phases: the pre-audit, audit window, and the audit itself.
Watch the video below for a quick answer to how long a SOC 2 audit itself takes.
Then keep reading to understand how long it takes to get a SOC 2 report with and without automation.
SOC 2 Type I Audit Timeline
Pre-Audit Phase Month 1 - Month 3
Step 1: Create policies
Step 2: Establish and document procedures
Step 3: Update internal processes
Step 4: Complete technical configuration remediation
Step 5: Train and educate employees
Audit Phase Month 4
Step 6: Begin the Type I audit
Step 7: Receive your SOC 2 Type I report
SOC 2 Type II Audit Timeline
Pre-Audit Phase Month 1 - Month 9
Step 1: Select SOC 2 Type I or Type II
Step 2: Define the audit scope
Step 3: Conduct a gap analysis
Step 4: Complete technical configuration remediation
Step 5: Collect documentation
Step 6: Complete a readiness assessment
Audit Window Phase
Step 7: Begin 3, 6, 9, or 12 month review period
Audit Phase Month 9 - Month 12
Step 8: Start the formal audit process
Step 9: Receive your SOC 2 report
How Long Does It Take to Get SOC 2 Compliance?
Pre-audit phase: 2 weeks-9 months
First, you’ll choose your report type, Type I or Type II, and select your Trust Services Criteria. You can include only Security or all five TSC. You’ll also determine the time frame and scope of your audit.
Next, you’ll assess the current state of your systems. Conduct a gap analysis to determine what you need to bring your controls in line with SOC 2 requirements.
Then you can work to close the gaps and compile the necessary documentation. You may also complete a readiness assessment to ensure you’re prepared. After passing the readiness test, you can start the SOC 2 audit process.

Audit Window Phase (Type II Report): 3, 6, 9, or 12 months
This is your audit window and will determine the period of time that’s covered in your final SOC 2 Type II report. This is when you’ll collect evidence and document how your controls are performing.
Audit phase: 1-3 months
Your auditor will set a list of deliverables and perform a series of control tests based on the Trust Service Criteria you’ve selected.
Next, your auditor will gather evidence, collect and review documentation, and interview members of your team.
Once they have the information they need, they'll write up your formal SOC 2 report. This report will include the auditor’s decision on whether you passed the audit.
The actual SOC 2 audit typically takes between five weeks and three months. This depends on factors like the scope of your audit and the number of controls involved.
How Compliance Automation Streamlines SOC 2
Traditional SOC 2 audits require a ton of prep work.
You have to write a bunch of policies, collect and organize hundreds of pieces of evidence, hunt down vendor security certificates, and do a slew of other tedious, time-consuming tasks. It's a slog.
Secureframe can make the entire audit process way more efficient.
We help companies get their SOC 2 in a fraction of the time — even compared to other compliance automation vendors.
Here's how:
Automated Evidence Collection
Our platform automatically collects evidence during your audit window. It also ensures you stay secure by alerting you of any vulnerabilities in your tech stack and telling you how to fix them.
Policy Libraries
Instead of writing a bunch of policies from scratch, you can choose from our library of templated policies and customize from there. They're all vetted and approved by ex-auditors and compliance experts.
Vendor Management
Instead of you requesting security certificates from all of your vendors, Secureframe fetches their security data for you. We'll also perform vendor risk assessments and provide detailed risk reports.
Audit Prep Dashboards
Assign tasks to individuals on your team and track your progress towards being audit-ready. You’ll get a real-time view of what’s looking good and what you can do to improve before bringing in an auditor.
Our customers have gotten ready for a successful SOC 2 audit in just a few weeks.
SOC 2 Audit Window FAQs
1. What is the industry standard window for a SOC 2 Type 2 report?
Typically, more mature enterprises settle into a 1 year Type 2 window for their SOC 2.
However, shorter windows for Type 2 reports are acceptable when first going through the compliance process, with the minimum window being 3 months. This allows organizations with an urgent need for a report to get their SOC 2 quickly.
If you don't have an urgent demand for a SOC 2 Type 2 report, consider at least a 6-month reporting window for your first report, since a longer window signals greater maturity in your security posture.
2. I'm new to SOC 2. How do I determine what the start date of my audit window should be?
The biggest consideration is the date you became "ready" for your audit, which includes implementing any remediation activities that were pointed out to you either during the readiness phase or the Type 1 audit phase.
When you go through a Type 2 audit, the auditor can sample any event, access, or change that existed starting from the first date of your window, so you want to make sure that you don't start the window until you're truly ready to be operating your controls. This means all key configurations are in place, and all processes are in place and followed for things like documenting new user access, etc.
3. I already have a previously issued SOC 2 Type 1 report. What should the start date of my Type 2 audit window be?
There are two considerations. First, if the auditor pointed out some controls in your Type 1 audit that you had to fix before your Type 1 date, then you should consider postponing your window until all of those items are fixed.
Second, if you didn't need to fix anything during your Type 1, you could consider starting your Type 2 window at a date earlier than your Type 1 date. This way the auditor could potentially leverage some of the audit work already done for the Type 1 report, reducing your time spent with the Type 2 auditor. You’ll need to talk with your auditor about whether this situation is feasible and fits their methodology beforehand.
4. I already have a previously issued SOC 2 Type 2 report. What should the start date of my audit window be this time around? Is it ok if there is a gap? Should there be a gap?
Generally, you should aim to have your next Type 2 window start the day after your first Type 2 ended. So, if you have a Type 2 report issued for the period January 1, 2021, to December 31, 2021, the best-case scenario is for your next period to be January 1, 2022, to December 31, 2022.
If you're not able to do this it's OK to have a gap. But you might have some explaining to do to key customers who review your report, so make sure you have a good explanation!
5. When I choose an audit window, am I then locked into that window for all subsequent years? Can I change my audit window, and when should I consider a change?
Your window can change year over year as you see fit. Generally, organizations settle into a routine that their customers come to expect.
Reasons to consider a change in timing might be:
- To extend your window (i.e., from a 3-month to a 12-month)
- To move your timing based on the needs of a client
- To align with other compliance initiatives such as ISO 27001, PCI DSS, SOC 1, SOX, etc,
- To add a new product in scope
6. What effect does switching auditors or compliance tools have on my SOC 2 Type 2 audit period?
A switch in auditor or compliance tool doesn't necessarily mean that any timing needs to change. However, depending on the circumstances that necessitated the switch, you should always consider whether your controls have operated seamlessly over the entire time period for your next Type 2 window. Be realistic about when your new Type 2 window should be so that your Type 2 report does not contain deviations.