A System and Organization Controls (SOC) report is like a letter grade in a restaurant window.
At a glance, it proves to your customers that you pay attention to crucial details. It includes detailed information on how well you safeguard customer data from unauthorized access.
But what is a SOC 1 and SOC 2 report, and how do you get one?
SOC 1 vs SOC 2 Report

A SOC 1 report is for organizations whose internal security controls can impact a customer’s financial reporting. Think payroll, claims, or payment processing companies. SOC 1 reports can assure customers that their financial information is being handled securely.
A SOC 2 report helps SaaS and service organizations prove their cloud and data center security controls.
Both SOC 1 and SOC 2 are attestation reports, where an organization’s management attests that certain information security controls are in place.
Then, an independent auditor accredited by the American Institute of Certified Public Accountants (AICPA) is brought in to verify those claims and either agree or disagree.
What is a SOC 2 Report?
At the end of a SOC 2 audit, the auditor issues a SOC 2 report. This report outlines their opinion on whether your company’s internal cybersecurity posture upholds SOC 2 security standards.
Remember, there’s no official SOC 2 certification — just the report with the auditor’s official opinion on the operating effectiveness of your service organization’s controls. Every organization that completes a SOC 2 audit receives a SOC 2 report, regardless of whether they passed the audit.
What’s included in a SOC 2 Report?
A final SOC 2 report includes several sections:
Management Assertion
The assertion section summarizes what company leaders told the auditor about their security and privacy controls. It explains whether the systems are represented fairly in the report. This section also describes whether your systems satisfy the Trust Service Criteria (formerly Trust Services Principles) you chose to include in your audit.
Independent Service Auditor’s Report
This section includes the auditor’s formal opinion about how well your controls perform against the TSC you selected.
- An “unqualified opinion” is a pass with flying colors.
- A “qualified opinion” means the company is almost compliant, but one or more areas aren’t there yet.
- An “adverse opinion” is a failure. The company falls short in one or more non-negotiable areas.
- A “disclaimer of opinion” means the auditor doesn’t have enough evidence to support any of the first three options.
System Overview
The system overview explains what your company does. It includes industry, location, and how you describe your infrastructure. It also includes a summary of your data security controls and why you’ve put them in place.
Infrastructure
This section outlines the organization's people, policies, processes, software, data, and technology. It also provides information on any third-party providers it outsources to.
Relevant aspects of the control environment
This part explains the most important aspects of your internal control environment. Examples include:
- Information systems
- Risk management and risk assessment policies/processes
- Monitoring strategies
Complementary user-entity controls
Complementary User Entity Controls (CUECs) are also known as User Control Considerations (UCCs). These are controls that organizations rely on their customers to implement.
Here’s an example:
Tons of companies use Dropbox or Google Drive to share files and collaborate.
But these file-sharing services don’t have a way to know who should be given access to certain company files. It’s up to Dropbox’s customer (the user entity) to keep track of who should have access. It’s also their responsibility to remove access for former employees or vendors.
Complementary subservice organization controls
The American Institute of CPAs defines a subservice organization as a supporting vendor. Some examples are data center hosting and transaction/data processing services. Depending on the type of service outsourced, your organization may want to include some of these sub-service organization’s controls in your audit.
Trust Services Criteria, Criteria Related Controls, and Tests of Controls
This lists each internal security control your company put in place, alongside the results of control tests.
Other information
Information provided by the company that the auditor decided was not relevant.
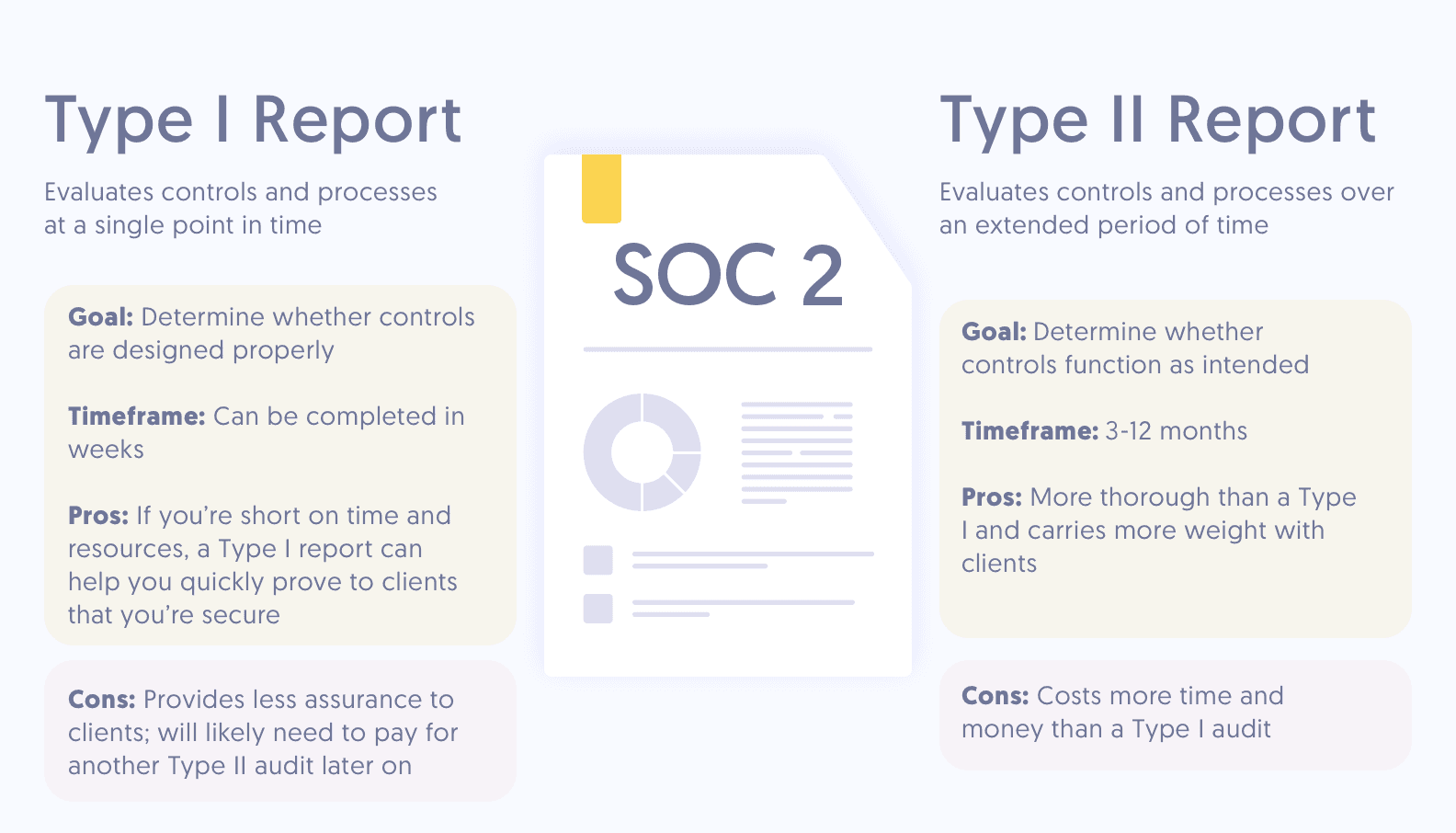
SOC 2 Report Types: Type I vs Type II Audit Reports
What’s in a SOC 2 Type I Audit Report?
SOC 2 Type I audits analyze an organization’s internal controls at a single point in time. It evaluates how well a company designed its internal security posture.
A SOC 2 Type I audit report provides an overview of the service organization’s system, controls, and processes as they relate to specific TSC.
Individual internal controls are linked to control objectives or Trust Services Criteria. Often, more than one internal control is linked to a single control objective.
The report also includes a description of the user entity controls needed for the system of controls to function as intended. If necessary, subservice organization controls are included as well.
Finally, Type 1 reports include a management assertion. This summarizes how the organization’s system and controls meet the control objectives.
What’s included in a SOC 2 Type II Audit Report?
Many of the aspects covered by a SOC 2 Type II audit are the same as those in a SOC 2 Type I audit. Both evaluate a company’s internal controls and processes as they relate to specific TSC.
The main difference between types of SOC reports is the period of time covered in the SOC audit and level of detail provided in the final report. While SOC 2 Type I audits examine a company’s controls at a single point in time, SOC 2 Type II audits analyze how well those controls perform over time.
As a result, the SOC 2 Type II audit report is more comprehensive than a Type I report and often provides a greater level of assurance for customers.
SOC 2 Type 2 reports cover everything in a Type I report. Plus details of the tests the auditor conducted to assess each control and the results. The report documents any exceptions as well.
SOC 2 Report Example
Download our illustrative example of a SOC 2 Type II Report to get a sense of what a report might include, how it might be organized, and how long it may be. This can help you if you're preparing for an audit or determining if a SOC 2 Type II report is the right choice for your organization.
Who Needs to See a SOC 2 Report?
Several stakeholders might need or want to read your SOC 2 report, including:
- Current and prospective customers want to know how you handle their sensitive data.
- Business partners want to know what kinds of internal controls are in place for data protection and to prevent costly data breaches.
- External auditors may need to examine internal controls surrounding customer data security.
- Potential investors need credible, reliable data about your company’s security and level of sophistication.
- Regulators may check to ensure your organization’s controls and systems comply with applicable laws and regulations.
Because the SOC 2 report includes such detailed information about a company’s systems and processes, most organizations and service providers that choose to share their SOC 2 report only do so under an NDA.
FAQs
What is the SOC 2 report?
The SOC 2 report attests to the design and operating effectiveness of an organization’s controls that are relevant to security, availability, processing integrity, confidentiality or privacy and helps establish trust between service providers and their customers.
What companies needs a SOC 2?
Any service organization that deals with sensitive information not related to financial reporting or that affects the operations of internal controls for its users (excluding financial operations) may need a SOC 2 report. This includes:
- Cloud service providers
- SaaS providers
- HR management services
- Recruitment platforms
- Host data centers
Is a SOC 2 Type 2 report confidential?
Yes, a SOC 2 Type 2 report contains confidential information, including detailed information about the organization’s system and controls and about the auditor’s tests, procedures, and results. That's why a SOC 2 report is a restricted use report and cannot be released publicly. If customers and prospects request to see this report, most organizations have them sign a non-disclosure agreement (NDA) first.