SOC 1® vs. SOC 2®: What’s the Difference and Which Do You Need?
Anna Fitzgerald
Senior Content Marketing Manager
Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Service providers that manage users’ sensitive information must provide structured documentation detailing what they’re doing to protect that information.
This is where SOC® examinations come into play. SOC stands for System and Organization Controls. It’s a type of examination geared toward entities that provide services directly related to a user’s control systems, like SaaS companies, financial reporting organizations, data centers, and payment processors.
There are different types of SOC reports designed to help service organizations meet specific user needs. In this post, we’ll discuss the main differences between SOC 1 and SOC 2 reports so you can understand which you might need.
SOC 1® vs SOC 2® report
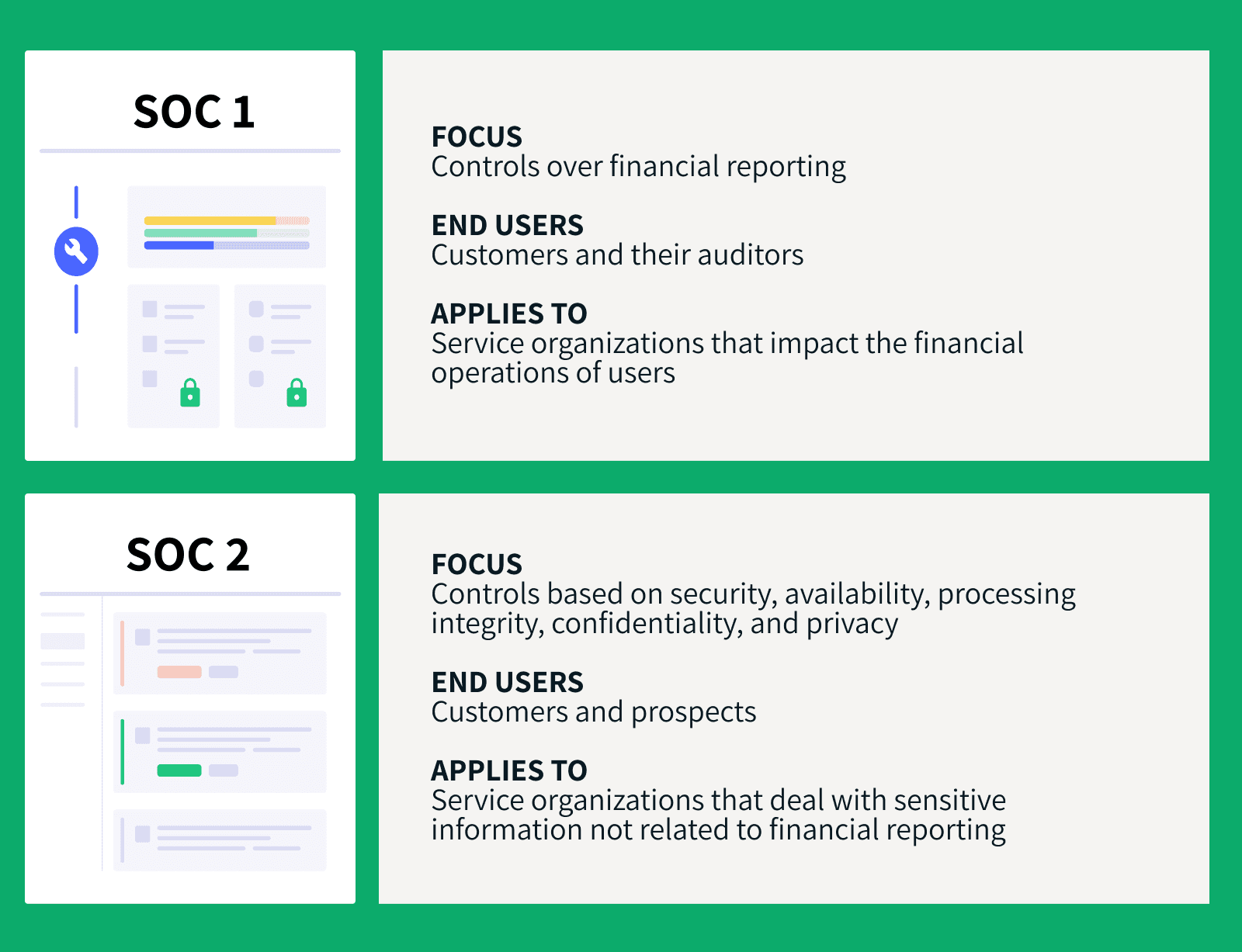
The key differences between a SOC 1 and SOC 2 report are the controls they examine and the user needs they meet.
SOC 1 examines a service organization's controls over financial reporting. Entities that use service organizations may request a SOC 1 report in order to evaluate the effect of those organizations’ controls on their own financial statements. This is important for the entities themselves and the CPAs that audit the entities’ financial statements.
SOC 2 examines a service organization's controls based on five criteria: security, availability, processing integrity, confidentiality, and privacy. This type of report may be requested by a broad range of users that need detailed information and assurance about a service organization’s controls relevant to 1) the security, availability, and processing integrity of the systems the organization uses to process users’ data and 2) the confidentiality and privacy of the information processed by these systems.
Let’s take a closer look at each report type below.
What is SOC 1®?
A SOC 1 report is an organizational controls audit that aims to analyze a service organization’s controls relevant to its users’ financial statements.
How to get a SOC 1 report
SOC 1 can be considered “attestation” reports, which means an external auditor (typically a CPA) must provide an opinion on the performance of your controls.
First, the organization’s management should define the controls that are directly related to user financial operations. Then, the CPA can analyze those controls and release an opinion on whether they’re effective.
Usually, this opinion includes:
- Scope: What is the scope of the engagement?
- Responsibilities: What are the responsibilities of the organization?
- Design: What is the design of the controls?
- Description: What is the description management provided regarding the controls?
- Type: What is the type of report being used?
- Opinion: What was the auditor’s opinion after conducting all the testing and examination?
Once you have this document in place, you can send it to your clients and stakeholders so they can use it whenever they’re going through a financial audit themselves.
The purpose of SOC 1 reports
If a company relies on a third-party service provider to perform crucial financial reporting processes (e.g., an outsourced payroll management system or a revenue reporting platform), they’ll probably ask those service providers for a SOC 1 report.
While these reports aren’t mandatory, they help you validate your controls and communicate to clients that you have secure processes. This will help them feel more secure and comfortable about their financial statements.
Types of SOC 1 reports
There are two types of SOC 1 reports:
- Type 2: A type 2 report evaluates the fairness of the management’s description of the service organization’s system and the suitability of the design and operating effectiveness of the controls to achieve the related control objectives included in the description throughout a specified period.
- Type 1: A type 1 report evaluates the fairness of the management’s description of the service organization’s system and the suitability of the design of the controls to achieve the related control objectives included in the description as of a specified date.
Who needs a SOC 1 report?
If your service impacts the financial operations of your users, then you probably need a SOC 1 audit.
For example, the following businesses may need to be SOC 1 compliant:
- Payroll processing software
- Billing management platforms
- Trust companies
- Financial reporting software
These are just a few examples. Bottom line, if you impact the financial information of users in some way, you need this.
What is SOC 2®?
Unlike SOC 1, which focuses on controls over financial reporting, SOC 2 examinations focus on the operations and compliance side.
SOC 2 reports are based on the Trust Services Criteria (formerly known as the Trust Service Principles) established by the AICPA. These are:
- Security (also known as “common criteria”): Is your service organization protected against unauthorized access?
- Availability: Are your services available at all times? Are services restricted?
- Processing integrity: Are your processing systems working reliably? Are they providing timely, accurate data to users? Do you process other organizations’ data? Do you have any integrations?
- Confidentiality: How are you managing confidential data? Is it classified and protected? Who can access such information?
- Privacy: Are you dealing with users’ sensitive, personal information? If so, what are you doing to keep that data protected?
Even though all these criteria are important when you’re trying to protect users’ sensitive information, the only one required for SOC 2 compliance is security. That’s why it’s called “common criteria.”
How to get a SOC 2 report
Like SOC 1, a SOC 2 is an attestation report where an external auditor needs to come in, analyze your controls, and issue an opinion report.
The AICPA provides no specific guidelines to prepare for a SOC 2 audit. It really depends on specific industry regulations and the type of service your organization provides. The best way to prepare is by analyzing how your services impact your users’ organizations and identifying which risks and potential issues are involved.
For example, if you’re a payment processing company for e-commerce businesses, you might want to consider the processing integrity principle in your controls. On the other hand, if your business provides HR management services, you may want to consider other principles, like confidentiality and privacy.
The AICPA doesn’t list specific controls you should have in place to comply with SOC 2, which can make the process more confusing.
At this stage, a readiness assessment can be helpful for figuring out the current status of your controls, spotting potential gaps in your systems, and better preparing for the actual audit.
Most accounting firms that have experience with SOC reports can perform readiness assessments to help you mitigate potential issues with your current controls prior to your SOC 2 examination.
The purpose of SOC 2 reports
Like SOC 1 reports, SOC 2 reports aren’t mandatory but they can help provide clients assurance that their data is adequately protected. This can help you build trust and transparency and get an edge over competitors.
Types of SOC 2 reports
Similar to SOC 1, there are two types of SOC 2 reports:
- Type 2: A type 2 report evaluates the management’s description of a service organization’s system and the suitability of the design and operating effectiveness of controls over an extended period of time.
- Type 1: A type 1 report evaluates the management’s description of a service organization’s system and the suitability of the design of controls at a specific point in time.
Who needs a SOC 2 report?
If your organization deals with sensitive information not related to financial reporting, then you may need a SOC 2 report.
For example, the following businesses may need to be SOC 2 compliant:
- Cloud service provider
- SaaS provider
- HR management service
- Recruitment platform
- Host data center
Add to this list any type of service-based organization that affects the operations of internal controls, excluding financial operations, for its users.
SOC 2 Compliance Kit
Get key assets you’ll need to get your SOC 2 report, including a compliance guidebook, customizable policy templates, readiness checklist, and more.
SOC® Type 1 vs Type 2
As we mentioned above, there are two types of SOC 1 and SOC 2 reports. That means once you’ve decided whether a SOC 1 or SOC 2 report is best for your organization, your next choice is deciding between a Type 1 and Type 2 report.
Both report types have some similarities, including:
- Objective: Both report types aim to explore a service organization’s controls
- Attestation: Both report types should provide an opinion from an external CPA
- Controls: Both report types should include the different controls used by the organization
But if you’re a service-based organization looking to become SOC compliant, it’s important that you understand the main differences between these report types.
In short, the main difference between Type 1 and Type 2 reports lies in the length and depth of the audit in question. Think of a Type 1 report as dipping your toes in the water, and Type 2 as going for a full swim.
Let’s explore this point a bit further.
Type 1 SOC reports
Type 1 SOC reports aim to explore the functionality of a service-based organization’s controls at a single point in time. For example, “audit report for November 30, 2021.”
Type 1 reports try to answer the question: Are your controls compliant for SOC 1 or SOC 2 right now?
This type of report usually covers whether your internal controls are properly designed according to the proprietary criteria of SOC 1 (control objectives) or SOC 2 (trust principles) in the context of the service you’re providing.
Some of the main components of a Type 1 SOC report include:
- Fairness: Auditor’s opinion on the fairness of management’s description of control objectives
- Suitability: Auditor’s opinion on the suitability of control design in the context of the service provided
- Performance: Auditor’s opinion on the performance of controls at a single point in time
Type 2 SOC reports
Type 2 SOC reports, on the other hand, aim to test the controls of a service organization in a range of time, typically six to 12 consecutive calendar months. For example, “audit report for the period of November 30, 2021, to May 30, 2022.”
For that reason, Type 2 SOC reports are much more comprehensive than Type 1 SOC reports and usually cover the continuous functionality of internal controls over longer periods. The SOC 2 Type 2 report therefore carries more weight and will give users more confidence in your processes.
Keep in mind Type 2 reports cover the exact same criteria as Type 1 (fairness, suitability, and performance). The only difference is that Type 2 reports explore the organization's controls over three to 12 months and provide more thorough descriptions of how each control performed.
Type 2 reports also add an extra section related to the tests performed by the service auditor on the operating effectiveness of such controls.
How can you choose the right report type?

Your client will often define the type of report you need for you SOC audit. What does your client need?
When users request a SOC report for their own auditing process, they typically want the most comprehensive version, and that is a Type 2 report.
But suppose you’re just getting familiar with SOC reports. In that case, whether it’s SOC 1 or SOC 2 — we suggest you start with a Type 1 report to get a better understanding of your organization’s controls, as well as knowing the auditing process first-hand.
If your client isn’t clearly asking for a Type 2 report, a Type 1 report will help you understand how the service auditor works and get help actually designing your organization’s controls. You’ll also be able to verify the accuracy of your controls description.
Getting a Type 1 SOC report first will help you prepare for Type 2 and set the right expectations for your team.
What if your client requests a Type 2 report? In that case, you’ll need additional testing from the auditor to ensure that you have the right controls in place. They will analyze whether these controls are working properly over the defined period.
In summary, Type 1 SOC reports are the best place to start because they help you design the right controls from the beginning. Type 2 SOC reports require you to already have such controls working over a long period of time.
Get industry insights, news & more in your inbox
Secureframe Insights is our monthly newsletter covering the latest cybersecurity and compliance news, insights, and events — from changing regulations to compliance checklists and more.
Join thousands of subscribers in getting these expert insights delivered straight to your inbox.

Deciding which SOC® report you need
Determining which type of SOC report you'll need mostly comes down to two factors: what controls you want examined and what user needs you’re trying to meet.
The table below shows the criteria for each type of report.
Whether you need a SOC 1 or SOC 2 report or both, Secureframe can help you streamline your SOC 2 process in weeks, not months. To learn more, read our product overview page or schedule a personalized demo today.
| SOC 1 | SOC 2 | |||
| What is covered? | Internal controls over financial reporting | Internal controls related to security, availability, processing integrity, confidentiality, and privacy of customer data | ||
| What user needs does it meet? | Users that need to evaluate the effect of their service organizations’ controls on their financial statements, plus the CPAs that audit those financial statements | Users that need detailed information and assurance about their service organizations’ controls relevant to security, availability, and processing integrity of the systems used to process their data and the confidentiality and privacy of the that processed data | ||
| What type of organization needs it? | Organizations providing a service that can impact a client’s financial statements | Organizations that store, process, or transmit any kind of customer data | ||
| What are examples of organizations that need it? | Collections agencies, payroll providers, payment processing companies | SaaS companies, data hosting or processing providers, cloud storage services | ||
| What are the types of report? | Type 1 | Type 2 | Type 1 | Type 2 |
| What does each type of report do? | Evaluates financial controls and processes at a single point in time | Evaluates financial controls and processes over an extended period of time | Evaluates controls and processes related to applicable TSC at a single point in time | Evaluates controls and processes related to applicable TSC over an extended period of time |
| What does the auditor’s opinion cover? | Determines whether financial controls are designed properly | Determines whether financial controls function as intended | Determines whether controls related to applicable TSC are designed properly | Determines whether controls related to applicable TSC function as intended |
FAQs
What is the key difference between SOC 1 and SOC 2 and SOC 3?
As you may already know, SOC reports can be split into three main categories:
- SOC 1: Focuses on service organizations' controls over financial reporting
- SOC 2: Examines a service organization's controls based on AICPA’s trust principles (security, availability, processing integrity, confidentiality, and privacy)
- SOC 3: Explores the same criteria of a SOC 2 report, documented for a more general audience (i.e., stakeholders)
What is the difference between SOC 2 Type 1 and 2?
The key difference is that a SOC 2 Type 1 report evaluates the suitability of the design of controls at a specific point in time, whereas a SOC 2 Type 2 evaluates the suitability of the design and operating effectiveness of controls over an extended period of time.
Do you need both SOC 1 and SOC 2 reports?
There are organizations that need both SOC 1 and SOC 2 reports. If you provide services that span across different industries, some clients may request a SOC 1 report and others may request a SOC 2.
What is the history of SOC reports?
Back in the 1990s, if a given organization wanted to inform users about internal controls, they could perform a Statement on Auditing Standards (SAS) No. 70.
A certified public accountant (CPA) would audit the organization's controls and release an opinion on their performance based on specific industry standards.
For years, SAS 70 was enough. But as organizations evolved, so did their complexity. Things like SaaS, infrastructure management, and information security came in. With them came the need for a better way to understand and audit an organization’s controls.
To deal with these changes, the American Institute of Certified Public Accountants (AICPA) released the Statement on Standards for Attestation Engagements No. 16 (SSAE 16), aiming to help technology-based service organizations report to users more efficiently and completely.
In June 2010, the AICPA got rid of the SAS 70 examination and introduced the idea of SOC reports, mirroring the International Standard on Assurance Engagements (ISAE) No. 3042.
According to the Sarbanes–Oxley Act (SOX), public companies must ensure their controls over financial reporting are secure and reliable. They’re fully responsible for it.
If a prospect or client suspects that your organization might harm their compliance status, they may not do business with you at all. That’s why SOC reports are so important.
What’s the purpose of SOC reports?
The main objective of SOC reports is to provide comfort to the user’s organization as it relates to security. This report can help users know that their processes and controls are in good hands.
By having an independent, third-party auditor examining your controls, your current users (or prospective users) can see that you’re operating in an ethical, safe way. This makes them more likely to trust your company with sensitive data.
Why do service organizations need SOC reports?
Tangibly proving to users that you’re doing everything right to protect their information and help them stay compliant is a true competitive advantage. And that’s just one of the many reasons you should consider becoming SOC compliant.
Other major benefits include:
- Improved prevention: Reduce risk and prevent unnecessary problems related to users’ integrity.
- Better positioning: Position yourself as an organization that’s ethical, reliable, and compliant.
- More control: Get more control over your processes and operations.
- Improve your processes: Find potential leaks in your controls and plug them before they start snowballing.
- Higher client retention and satisfaction: Build trust with your clients and make them feel comfortable working with you.

Anna Fitzgerald
Senior Content Marketing Manager
Anna Fitzgerald is a digital and product marketing professional with nearly a decade of experience delivering high-quality content across highly regulated and technical industries, including healthcare, web development, and cybersecurity compliance. At Secureframe, she specializes in translating complex regulatory frameworks—such as CMMC, FedRAMP, NIST, and SOC 2—into practical resources that help organizations of all sizes and maturity levels meet evolving compliance requirements and improve their overall risk management strategy.

Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Rob Gutierrez is an information security leader with nearly a decade of experience in GRC, IT audit, cybersecurity, FedRAMP, cloud, and supply chain assessments. As a former auditor and security consultant, Rob performed and managed CMMC, FedRAMP, FISMA, and other security and regulatory audits. At Secureframe, he’s helped hundreds of customers achieve compliance with federal and commercial frameworks, including NIST 800-171, NIST 800-53, FedRAMP, CMMC, SOC 2, and ISO 27001.