Security Questionnaire: How to Answer and Send Your Own [+ Free Template]
Anna Fitzgerald
Senior Content Marketing Manager
Cavan Leung
Senior Compliance Manager
Security questionnaires are an important part of a company’s due diligence process. When used well, they can help your organization build trust with new prospects. But they can be time-consuming if you don’t have efficient processes in place.
In this guide, we’ll walk you through:
- How to answer a security questionnaire and simplify the process
- Important topics to include when sending your own security assessments, and key questions to ask
If you need inspiration for sending your own assessment, check out our security questionnaire template.

What is a security questionnaire?
A security questionnaire is a list of questions that assess your organization’s security and data privacy practices. Organizations often exchange questionnaires before going into business together.
While you can create your own questionnaire to learn about a company’s security posture, there are also standardized questionnaire templates available like the Standard Information Gathering (SIG) questionnaire.
The questions may vary but security questionnaires are a standard part of the third-party risk management process.
Imagine you’re the CISO of a growing SaaS company. You’re about to sign up with your first strategic partner. One day, they send you a list of questions:
“Has your organization ever been compromised?”
“Does your organization use a local firewall?”
“Do you have a data center? Where is it located?”
Congratulations — you’ve received your first security assessment questionnaire. They may appear intimidating, but they can be an invaluable tool for your organization.
Let’s take a closer look at the purpose of a security questionnaire, then walk through the process of answering one so you can close new deals.
Recommended reading
Vendor Risk Management (VRM): How to Implement a VRM Program that Prevents Third-Party Breaches
Why did you receive a security questionnaire?
If your IT security or sales team received a security questionnaire, it means that another organization is considering doing business with you. But first, you need to show that your organization can be trusted to protect sensitive data.
Answering assessments can take up valuable time, even more so if you’re receiving multiple questionnaires from a growing list of potential customers.
As your organization grows, you’ll want to have a standardized process for answering questionnaires.
How should you answer a security questionnaire?

While security questionnaires are an important part of TPRM, the time spent answering them can add up if you’re not strategic.
We’ll walk you through how to use compliance audits and reports to simplify the answering process. For further simplification, we’ll guide you on how to build a knowledge database and keep your answers concise.
If you discover a security gap when answering a questionnaire, don’t worry. We’ll show how that can be a growth opportunity for your organization.
Here’s how to answer a security questionnaire in four easy steps.
Step 1: Use your compliance frameworks and privacy certifications
Compliance frameworks like SOC 2® or ISO 27001 certifications will prepare your team to address most security questionnaires.
To illustrate how this works, let’s examine preparing for a SOC 2 audit.
To pass you must:
- Test the effectiveness of your infrastructure, data, risk management policies, and software
- Establish that you meet one or more of the SOC 2 Trust Services Criteria: Security, plus availability, processing integrity, confidentiality, and/or privacy
- Gather evidence of security controls and security policies
- Run readiness assessments
- Perform a gap analysis and close each gap
You can save time on future questionnaires by completing the groundwork here.
Tip: Use your certifications to create standardized documentation of your verified data security practices.
Step 2: Create a centralized knowledge base
You can build a knowledge database when your organization meets the criteria for various compliance frameworks.
As you receive more vendor assessments, log each question and answer into a centralized database. Then you can make a habit of monitoring and updating the knowledge base.
Tip: Reference and repurpose relevant answers from your knowledge base for fast and consistent responses on future assessments.
Step 3: Keep answers short, simple, and direct
It’s common for a security assessment to include hundreds of questions. Below are a few things reviewers expect:
- Direct and complete responses: Follow instructions regarding answer length and use active and concise language.
- Honest answers backed by proof: Avoid answering “yes” to any questions if implementation is in the works. Expect clients to ask for proof and communicate honestly to avoid sounding evasive.
- Unique answers that don’t repeat: Similar questions may appear on the questionnaire. Avoid copy and pasting answers to save time.
Tip: Before answering questions, scan the list for any that are not applicable to your product or service. This can help narrow down the questions you might need to spend more time on by providing further explanation.
Answering each question should also help your organization define its cybersecurity practices. They can even help you uncover any internal security vulnerabilities that could lead to a data breach.
Step 4: Prepare a remediation plan
Don’t panic if you uncover a security gap when completing a questionnaire. Instead, you can show your potential business partners that you’re a proactive and transparent organization. Here’s how:
- Prepare a remediation plan to align your security practices with customer expectations
- Provide a timeline for when you will have met your customer’s security standards
Tip: Keep lines of communication open and your customer informed about how your information security upgrades are going.
Now that you know how to prepare for and answer a security questionnaire, the next step is to create and send your own assessments.
Automate your security questionnaires
Save hundreds of hours answering questionnaires and RFPs with Secureframe’s machine learning-powered automation.
Why should you send a security questionnaire?
Organizations can practice continuous compliance by sending security questionnaires. This could also be a competitive advantage for your organization.
According to a Ponemon Institute report, only 49% of organizations vet third-party vendors. Half of your competitors allow vendors access to sensitive information without due diligence.
Sending security questionnaires also makes adhering to data protection regulations less expensive. Research shows non-compliance costs organizations roughly three times as much as compliance. Vetting your potential third-party vendors can literally pay for itself.

When growing your organization, sending questionnaires helps build trust with new business associates. Sending annual assessments shows that you are proactively managing third-party risk. It also signals that you are safe to work with.
There are certain topics your security questionnaire should cover that can help you close more deals.
Which topics should a security questionnaire include?
The content of security questionnaires varies by organization. But they all have the same goal: vendor security. You want to find out if you can trust a prospective service provider to protect your business and customer data. Including the following topics should help you find out.
Security and privacy certifications
Asking about security and privacy certifications is a great place to start. See if a potential business associate has any of the following certifications:
- SOC 2
- ISO 27001
- PCI DSS
- HIPAA (if you handle protected medical data)
- GDPR and/or CCPA (if you handle personal data for European Union and/or California residents)
These credentials show that your counterpart is maintaining compliance with data protection standards.
It can be simple as asking:
- Can you provide proof of a SOC 2 Type 1 or Type 2 report?
- When was your last ISO 27001 audit?
GRC management
Next you will want to see how a potential vendor handles governance, risk, and compliance (GRC) before entering an agreement. You want to know that your business associate has a strategy for managing risk and maintaining compliance. Are they able to balance GRC while meeting their performance goals?
Here are some good questions to help make that determination:
- What is your security team's incident response policy?
- What is your mean time between failures?
- How often does your organization conduct a risk assessment?
Continuous compliance
Organizations that conduct regular internal compliance audits have lower adherence costs. Non-compliance is expensive, so you want to partner with an organization that is always looking for its own compliance gaps.
To find out if your third parties follow continuous compliance, ask about their:
- Policy management
- Vendor management
- Vulnerability management
- Incident management
- Data management
- Risk management
- Business continuity management
- HR management
Questions you can ask include:
- Do you train your employees on detecting cyber attacks?
- How do you conduct vulnerability analyses?
- Do you use a third-party vendor for data storage? If yes, what is your third-party risk management strategy?
Network security
You may want to understand how an organization protects its network infrastructure to see if there are cybersecurity vulnerabilities or any potential gaps that can be exploited.
Questions you can ask include:
- Do you use an intrusion prevention system or intrusion detection system?
- Are industry-standard firewalls deployed? Where?
- Do you have audit logs for all systems that store or process critical information?
Physical security
Similarly, you may also want to know how an organization protects its physical infrastructure, including any data centers, workspaces, or facilities. This can help you identify potential weaknesses and threats to assess whether the infrastructure is adequately protected against threats such as burglaries, data breaches, and unauthorized access.
Questions you can ask include:
- Are there physical access controls in place for securing servers and desktop machines?
- Do you have a data center? If so, what are the physical security measures of your data center?
- What is your process for destroying sensitive data?
Now that you’re ready to send your own, here’s how to make the process painless for you and your customer.
How to create an effective security questionnaire
Creating an effective security questionnaire is imperative to identifying vulnerabilities posed by third-party vendors. Here are some tips that can help:
1. Reference an industry-standard questionnaire.
Every organization is unique so it’s good practice to reference the following industry-standard questionnaires before building your own:
- Standard Information Gathering (SIG) Questionnaire
- Consensus Assessment Initiative Questionnaire (CAIQ)
- CIS Critical Security Controls (CIS)
- NIST SP 800-30
Recommended reading: https://secureframe.com/blog/sig-questionnaire
Recommended reading

How to Use SIG Questionnaires for Better Third-Party Risk Management
2. Start with a template.
Rather than building a security questionnaire from scratch, consider using an auditor-reviewed security questionnaire template (like the one below) that lists possible questions covering administrative safeguards to severance of services.

Security Questionnaire Template
Use this auditor-approved security questionnaire template to evaluate vendor security practices.
3. Customize the questionnaire to each vendor.
Industry-standard questionnaires and templates cover many of the questions you need to ask to gauge a vendors’ security posture, but they are not enough to defend against the unique risks of your third-party attack surface.
Each questionnaire should contain questions about the unique threats your organization as well as the vendor faces and any compliance requirements that are specific to your or their industry.
Are security questionnaires enough to manage third-party risk?
Security questionnaires can be a valuable tool in managing third-party risk, but they should not be the only tool. Here are a few reasons why questionnaires are only one potential aspect of an entire third-party risk management program:
- Limited scope: Questionnaires typically focus on asking vendors about their security measures and practices. While this provides valuable insight, it may not uncover all potential risks associated with the vendor's products or services.
- Lack of verification: Responses to questionnaires may not always reflect the true state of a vendor's security posture. Vendors might provide inaccurate or incomplete information, often unintentionally. Without independent verification, it's challenging to confirm the accuracy of the information provided in the questionnaires.
- Point-in-time assessments: Risk is not static; it evolves over time. So even if a vendor's security posture appears satisfactory at the time of assessment, it could change due to various factors such as changes in the threat landscape, the introduction of new vulnerabilities, or internal organizational changes.
For these reasons, effective third-party risk management requires a multi-faceted approach that goes beyond questionnaires. This may include:
- Audit results or compliance documents like a SOC 2 report
- Contracts
- Regular risk and security assessments
- Continuous monitoring to ensure ongoing compliance and risk management.
Recommended reading

SOC 2 vs Security Questionnaires: What’s the Difference & Which Do You Need?
In conclusion, while security questionnaires can be a valuable component of third-party risk management, they should be part of a broader risk management strategy that includes risk assessments, ongoing monitoring, and collaboration with vendors to mitigate risks effectively.
Secureframe Third-Party Risk Management (TPRM) can help streamline the way organizations handle third-party risks, offering a comprehensive suite of tools to make third-party risk management more efficient than ever. This includes:
- Centralized view of entire TPRM program: In the Secureframe platform, you’ll see an inventory of all active and archived vendors, complete with their risk levels. Each vendor has a detailed profile containing information about their services and security compliance, including authentication methods and audit results, ensuring comprehensive vendor oversight.
- Streamlined risk assessments: Admins can evaluate a vendor’s risk based on the data and environments they access, and all relevant documents, such as compliance reports and policies, can be attached to the vendor’s profile for easy access. You can perform detailed risk assessments for every vendor by reviewing the data and environments they access and all relevant documents, such as compliance reports and policies, in one place.
- Continuous monitoring: You can assign owners to each vendor, and schedule annual or one-time reviews to ensure ongoing risk management and compliance throughout the vendor relationship.
- Comply AI for TPRM: Comply AI for TPRM can streamline the security assessment process by automatically extracting answers to internal security review questions from documents that were uploaded to a vendor’s profile, like a SOC 2 report. This saves you time, reduces manual effort, and enhances the efficiency of security reviews.
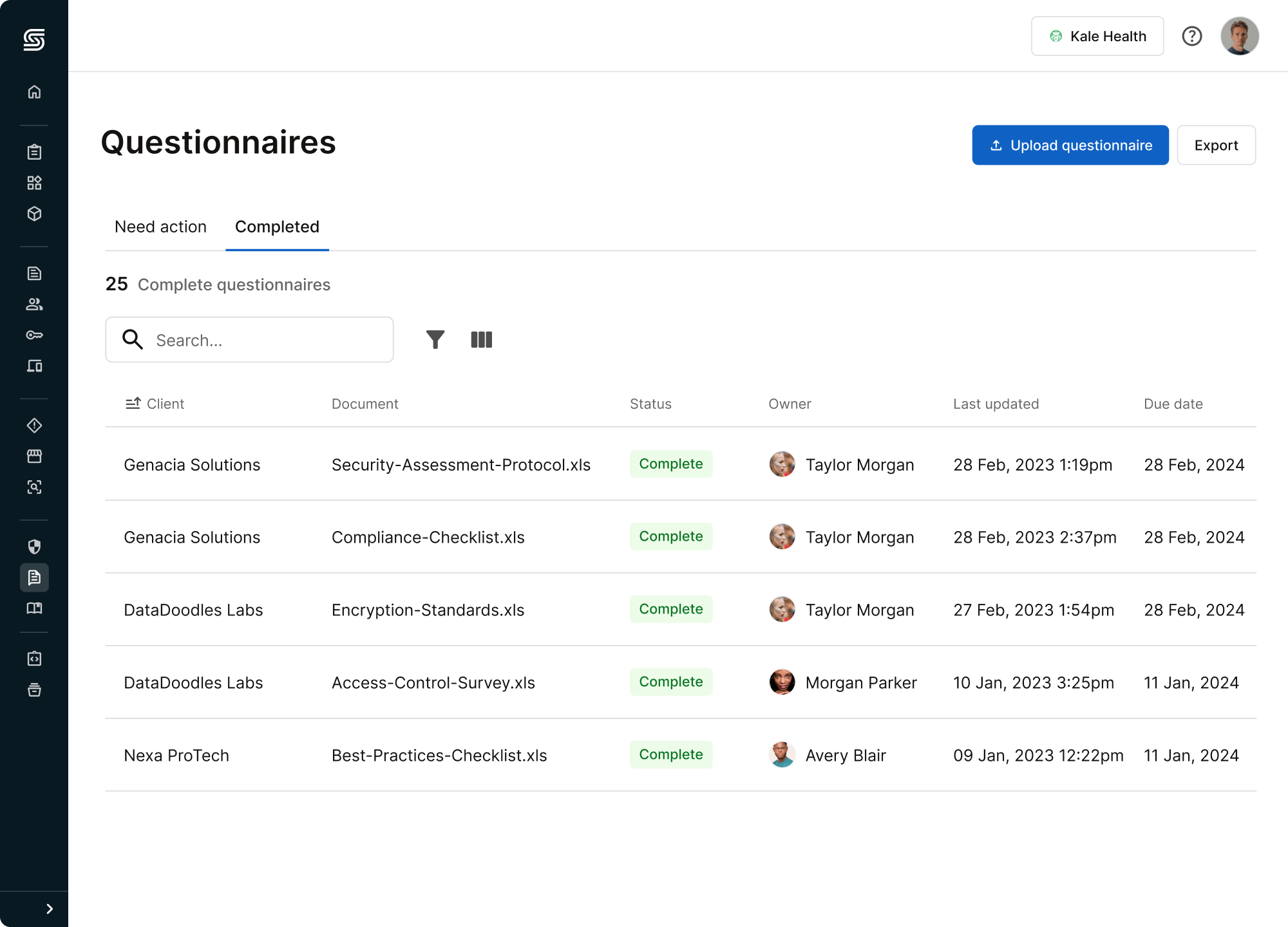
How Secureframe’s security questionnaire automation works
Filling out security questionnaires by hand can take hundreds of hours in aggregate each year. They can also be expensive if you need to hire outside consultants and subject matter experts to help you answer detailed questions.
That’s why we built Questionnaire Automation, an AI-powered solution that makes it fast and easy to respond to customer questions and demonstrate your organization’s security posture.
Upload the security questionnaires you receive to Secureframe, then tag the question and answer fields. Our machine learning will fill in the answers. Verify the answers or assign to your internal SMEs to edit details, then export the completed questionnaire in the original format and send it back to your customer.
Now you can easily access answers to security questions from the comfort of your browser with the Knowledge Base Chrome Extension.
Schedule a demo of Secureframe Questionnaire Automation to see it in action, and to learn how our compliance automation platform can streamline your security compliance program.

FAQs
What is a security questionnaire?
A security questionnaire is a list of questions designed to assess an organization’s security and data privacy practices. By understanding the security posture of third party vendors, organizations can make informed decisions about risks and ensure that partners and suppliers don't introduce vulnerabilities into their environment.
How do you complete a security questionnaire?
When completing a security questionnaire make sure to give accurate, up-to-date answers.
- Review the complete questionnaire to understand its purpose and scope.
- Gather input from stakeholders across the organization, including IT, legal, HR, and operations. Answer questions honestly and accurately. If you don’t know the answer, don’t guess, and if the question isn’t applicable to your organization, explain why.
- Include evidence when necessary. Some questions might require you to offer evidence such as policies or screenshots. Be sure to send up-to-date documents and redact any sensitive information that isn’t relevant to the questionnaire.
- Before submitting, review the responses to ensure accuracy and consistency. It’s also good practice to keep a copy for your own records.
Security questionnaire automation streamlines the process and saves hours of manual work by automatically completing answers to security questionnaires and RFPs based on past responses.
Why are security questionnaires important?
Security questionnaires are an essential part of a strong vendor risk management program:
- Risk management: Questionnaires help organizations assess and manage third-party risk.
- Regulatory compliance: Many frameworks require organizations to ensure partners and suppliers adhere to specific regulations to maintain compliance.
- Customer trust: Completing security questionnaires demonstrates transparency and proves an organization is proactive about implementing strong data security and privacy practices.
- Improve security: Filling out a questionnaire can help organizations uncover gaps in their security posture and be proactive about mitigating risks.
What is the best security questionnaire automation?
Secureframe’s security questionnaire automation leverages the latest advances in artificial intelligence (AI) and machine learning to pull the best answers for security questions based on past responses, saving hours of manual work completing questionnaires and RFPs

Anna Fitzgerald
Senior Content Marketing Manager
Anna Fitzgerald is a digital and product marketing professional with nearly a decade of experience delivering high-quality content across highly regulated and technical industries, including healthcare, web development, and cybersecurity compliance. At Secureframe, she specializes in translating complex regulatory frameworks—such as CMMC, FedRAMP, NIST, and SOC 2—into practical resources that help organizations of all sizes and maturity levels meet evolving compliance requirements and improve their overall risk management strategy.

Cavan Leung
Senior Compliance Manager
Cavan Leung, CSSK, CISA, CISSP is an information security leader with over a decade of experience in the security, privacy, and compliance industries. A former auditor and security consultant, Cavan performed ERP and SOX compliance audits at Deloitte, as well as SOC 1, SOC 2, GDPR, and ISO 27001 compliance assessments for Fortune 500 companies at Schellman. At Secureframe, he’s helped hundreds of customers achieve compliance with SOC 2, ISO 27001, GDPR, HIPAA, and more.