
30 Recent Cyber Attacks & What They Tell Us About the Future of Cybersecurity
Anna Fitzgerald
Senior Content Marketing Manager
Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Cyber attacks more than doubled in 2025, with Health-ISAC’s 2025 Fourth Quarter Health Sector Heartbeat reporting a 55% year-over-year increase in cyber incidents.
While attacks continue to grow in frequency, the more alarming shift is in their impact. As attacks against governments and critical infrastructure like healthcare and manufacturing are intensifying in both scale and ambition, the cybercrime losses are staggering. According to the FBI’s 2025 Internet Crime Report, US cybercrime losses hit a historical high of nearly $21 billion, a 26% YoY increase.
We’ve analyzed recent cyber attacks within the past 6 months and a larger sample within the past 5 years to identify important patterns, trends, and actionable takeaways that can help organizations understand emerging threats and shifting criminal tactics and improve their resilience to help prevent cyber attacks.
Recent Cyber Attacks 2026
This year marks a noticeable escalation in cyber attacks against the defense industrial base (DIB), government agencies, and critical infrastructure providers. More adversaries are shifting from direct and often opportunistic attacks for the purposes of quick financial gain, immediate disruption, and traditional espionage toward sophisticated, persistent operations that target trusted, widely-used tools in order to:
- compromise supply chains
- disrupt operations and production capacity on a global scale, and
- maintain a long-term foothold for ongoing data theft, sabotage, and economic damage.
Below are eight of the most notable cyberattacks so far this year, their impacts, and what organizations can learn from them.

1. Iranian cyber attacks on OT devices across U.S. critical infrastructure
Date: April 2026
Impact: Disruptions to U.S. critical infrastructure and financial loss
According to an advisory issued jointly by several government agencies including the FBI, CISA, and NSA in early April, Iran-affiliated advanced persistent threat (APT) actors began launching an attack targeting internet-facing operational technology (OT) devices, including programmable logic controllers (PLCs) manufactured by Rockwell Automation/Allen-Bradley used to control critical sectors.
The FBI reported that this attack resulted in financial loss and operational disruption across several U.S. critical infrastructure sectors including water utilities, energy networks, and local government facilities.
According to a report from Censys, this APT campaign threatened more than 5,000 industrial control devices around the world, including roughly 3,900 in the U.S.
Key learning
As a result of these escalating campaigns targeting OT operators, a group of U.S. government agencies released a new publication dedicated to supporting critical infrastructure organizations in applying zero trust principles to their OT environments.
Zero trust is a critical shift in enterprise network security that focuses on:
- defending users, assets, and resources themselves, instead of network segments
- limiting threat actor movement and potential damage, instead of preventing entry
While this publication is just one of the latest examples in decades-long effort to get federal agencies and critical infrastructure organizations to embrace zero trust principles, this is particularly important for OT operators since many use legacy technology, lack adequate resources and budgets for cybersecurity, and are less tolerant of disruptions than IT environments, which makes zero trust even more challenging to implement.
However, those that do invest in transitioning to zero trust architecture can help mitigate the risk of losing visibility or control of critical systems that affect the nation’s ability to provide energy, water, transportation, communications, and more and the catastrophic outcomes of such cyber incidents.
Recommended reading

What Is Zero Trust Architecture & Why Does It Matter for CMMC Compliance?
2. UnsolicitedBooker advanced persistent threat attacks
Date: January 2026
Impact: Backdoors deployed to establish footholds in telecommunications environments in Central Asia
Starting in early 2026, the China-aligned advanced persistent threat (APT) group UnsolicitedBooker began launching highly tailored spear-phishing campaigns against telecommunications providers in Central Asia, specifically targeting organizations in Tajikistan with rare and technically sophisticated backdoors. These attacks indicate a high level of operational maturity and a clear focus on persistent access, data exfiltration, and lateral movement within targeted telecom environments.
While the impact of these specific attacks is unclear, Rescana researchers say the APT group’s targeting of telecom providers is likely due to the strategic value of intercepting communications and accessing sensitive subscriber data.
Researchers also warn that their current focus is on Central Asia, but UnsolicitedBooker has proven that they are capable of rapidly shifting its targeting to other regions and sectors, including government, defense, and critical infrastructure.
Key learning
Disruptive and destructive cyber attacks in critical sectors carried out by advanced adversaries known as advanced persistent threat (APT) groups are on the rise globally, with the US alone experiencing a 136% surge in APT attacks in the first quarter of 2025. The objective of these groups isn’t typically a quick ransomware payout. It’s to disrupt operations, gain intelligence, and position themselves for future sabotage.
As organizations expand their digital footprints, rely heavily on complex supply chains, and operate under increasingly interconnected federal and global regulations, the risk—and potential fallout—of APT attacks continues to rise. It’s therefore essential that organizations, particularly those in critical infrastructure, improve the detection and prevention of these threats.
Recommended reading

Why Advanced Persistent Threats (APTs) Are Increasing & What to Do to Prevent Attacks
3. Stryker cyber attack
Date: March 2026
Impact: Global disruption to business operations, material impact on its first quarter earnings, and lawsuits related to theft of employee data
On March 11, the medical technology giant Stryker suffered a cyber attack that temporarily disrupted its manufacturing, ordering, and shipping capabilities. Operational disruptions across its global network and supply lines resulted in several cascading effects, including some health systems having to delay surgical procedures that hinged on Stryker’s ability to deliver patient-specific products. Stryker announced it was fully operational on April 3, although it was still ramping to peak production capacity.
The incident has had a material impact on its first quarter earnings, and resulted in legal action over the theft of sensitive employee data. As of April 2, six lawsuits had already been filed by employees who claim the company failed to protect their personal data.
Key learning
As a leading maker of medical devices used by the US military as well as many other organizations, Stryker has a contract with the Defense Logistics Agency that likely includes CMMC requirements. Incident response is one of the most important domains in CMMC. Implementing these requirements is essential to improve how organizations detect, contain, and recover from security events that impact sensitive information and mission-critical operations.
Contractors that fail to meet these requirements may face severe consequences, including contract loss and legal consequences under the False Claims Act.
Recommended reading

CMMC Incident Response Requirements: How to Build a Compliant Incident Response Plan [+ Template]
4. Trivy supply chain attack
Date: March 2026
Impact: Trivy ecosystem supply chain temporarily compromised
On March 19, a widely used GitHub Action for running Aqua Security’s Trivy, one of the most widely used open-source vulnerability scanners, was compromised for approximately 12 hours in a multi-phase supply chain attack.
Leveraging access from a prior incident that was not fully remediated, threat actors injected credential-stealing malware into official releases of Trivy and simultaneously compromised trusted security tooling, including a widely used GitHub Action for running the Trivy vulnerability scanner.
This compromised tooling was designed to execute credential-harvesting logic in addition to the legitimate Trivy functionality so workflows and scans appeared successful while CI/CD secrets were exfiltrated, resulting in a cascading breach across environments.
Because credential theft was combined with tag poisoning, binary tampering, persistent backdoors, and a self-propagating worm, it’s been described as “the most sophisticated supply chain attack on a security tool to date.”
Key learning
Organizations today have sprawling supply chains that significantly increase their attack surfaces. They need a systematic way to evaluate which relationships introduce acceptable risk and which ones create potential points of failure that must be addressed.
A supply chain risk assessment is the structured process for identifying, analyzing, and evaluating potential threats, vulnerabilities, and impacts introduced by any part of your supply chain, including third-party suppliers, vendors, contractors, service providers, and components, such as hardware or open-source software like Trivy.
Recommended reading

Supply Chain Risk Assessment: How to Actually Evaluate Third-Party Risk in 2026 + Template
5. New Britain ransomware cyber attack
Date: January 2026
Impact: Disrupted city network systems for more than 48 hours, forcing departments to operate with pen and paper
A ransomware attack that started on January 28 disrupted New Britain’s city network systems, including police and fire departments, for more than 48 hours. With the internet down, departments had to operate with pen and paper while federal authorities investigated the suspected cyber attack.
In April, three months later, city officials said New Britain is still recovering from the attack.
Key learning
While New Britain was able to continue to deliver essential services, including public safety services, it had to resort to manual processes in some cases. And months into recovery, it’s still unclear whether personal or confidential information stored on the city’s server was impacted.
This underscores how important it is for local municipalities as well as private sector organizations to understand that the question isn’t if their organization will face a disaster. It's if they’ll be prepared when it happens.
Recommended reading

The Disaster Recovery Gap: 110+ Statistics Revealing Why 80% of Orgs Aren't Prepared & What It’s Costing Them
6. Seedworm APT attacks
Date: February 2026
Impact: Infiltrated US infrastructure and defense supply chain networks
Earlier this year, an Iran-affiliated APT actor Seedworm launched a cyber campaign that affected a range of sectors and countries.
Due to backdoors and malware discovered by Symantec researchers, Seedworm is suspected to have infiltrated a US bank, an airport, several non-governmental organizations in both the US and Canada, and a software company that supplies the defense and aerospace industries, among others.
Researchers observed an attempted data exfiltration from this software company, although they’re unsure if the exfiltration was successful. Other outcomes of this cyber attack remain unclear, but security analysts at Symantec warn that it is likely part of a broader effort to establish footholds in strategically relevant networks for the purposes of spying, information gathering, compromising key systems, and launching further attacks.
Key learning
As activity targeting government, transportation, energy, defense contractors, and related supply chains increases, defense subcontractors can expect pressure to meet CMMC requirements from prime contractors to intensify.
Many primes are enforcing CMMC ahead of government implementation timelines, requiring subcontractors to demonstrate CMMC Level 2 (C3PAO) certification or readiness even though Phase 2 of the government rollout begins November 10, 2026.
Recommended reading

How Are Primes Tracking CMMC Across Their Own Supply Chains? A Deep Dive into Boeing’s ESLC
7. Trellix data breach
Date: May 2026
Impact: Unauthorized access to portion of source code repository
In May, Trellix disclosed a data breach after attackers gained access to "a portion" of its source code repository. At the time of disclosure, Trellix said it had yet to find evidence that the threat actors have exploited or altered the source code they accessed.
However, as a global cybersecurity company that provides services to over 50,000 business and government customers worldwide, the potential impact of this breach for downstream customers is significant.
Key learning
The software supply chain is an attractive attack vector, particularly for the Defense Industrial Base or other government agencies. Rather than trying to breach a major defense contractor or government agency directly, adversaries have increasingly focused on software vendors those organizations depend on. Compromise one vendor with a broad base of government and DIB customers and you potentially have access to dozens or hundreds of federal contractors and agencies at once.
That’s why understanding and managing software supply chain risk is critical to complying with federal frameworks like CMMC and to building operational resilience.
Recommended reading

Software Supply Chain Security in the Defense Industrial Base: What's Inside the Code You're Running?
8. Instructure data breach
Date: April 2026
Impact: Data breach of 3.65TB affecting 275 million teachers and students
Education technology company Instructure disclosed a cyber attack on April 30 that disrupted its services and tools, including Canvas, one of the most widely used learning platforms across 9,000 educational institutions and other organizations. The attack also resulted in a data breach.
The extortion group ShinyHunters claims it was behind the attack, and stole 3.65 terabytes of data belonging to 275 million students, teachers, and other individuals worldwide.
Key learning
This is the latest in a string of cyber attacks in the education sector that have made headlines, including attacks on Harvard University, Princeton University, and the University of Pennsylvania in late 2025. While data breaches in general reached an all-time high last year, the education sector was particularly hit hard, with cyber attacks surging 63% year-over-year.
Recommended reading

Biggest Data Breaches of 2025: Common Attack Vectors and How to Protect Your Business in 2026
Why we include cyber attacks from the past 3 years
While many cybersecurity news feeds highlight only the most recent breaches, we include attacks from the past two years so we can:
- Understand the root cause and contributing factors
- Share takeaways after full investigations conclude
- Accurately assess the true impact, including remediation and costs
- Avoid highlighting ongoing incidents that attackers could still exploit
Looking back at major attacks with the benefit of hindsight helps organizations learn from what went wrong and build stronger defenses. With this in mind, let’s look at some of the biggest cyber attacks in the last three years.
Recent Cyber Attacks 2025
In 2025, cyberattacks became more sophisticated, faster to execute, and impacting more sectors.
The incidents below reveal several patterns worth noting:
- A single threat group (Scattered Spider) executed coordinated campaigns across insurance, retail, and aviation in the same quarter, demonstrating how adversaries now operate at industrial scale across sectors.
- Ransomware operators and nation-state actors alike shrank their attack timelines from days to hours.
- The line between cybercrime and espionage continued to blur, with defense contractors, federal software vendors, and critical infrastructure all targeted in the same year.
Together, these incidents paint a picture not just of increasing volume, but of increasing strategic intent.
9. Opexus insider threat attack
Date: February 2025
Impact: Government system outages and deletion of dozens of government databases and thousands of files
Opexus, a major software service contractor for the U.S. government, experienced an insider threat attack in early 2025.
Since Opexus handles sensitive data for nearly every U.S. federal agency, the insider attack resulted in a massive federal data breach, with two employees allegedly destroying 30 government databases that contained data from the General Services Administration and exfiltrating approximately 1,800 files related to one government project. An investigation also uncovered that these malicious insiders caused an outage of two key software systems used by government agencies to process and manage their records, and in some cases a permanent loss of data.
Key learning
This breach highlights growing software supply chain threats, particularly for federal governments. As a result of vendor breaches like these, many government agencies are tightening cybersecurity requirements and enforcement across their supply chains.
While the DIB is in the middle of its phased implementation of CMMC requirements contractually, the General Service Administration (GSA) released its own CUI framework earlier this year. Because of its differences from CMMC, this release has raised concerns about the patchwork of cybersecurity requirements that some federal contractors will have to navigate.
However, the bigger takeaway is that increased assurance of cybersecurity compliance is becoming an integral part of federal procurement so federal contractors must prioritize implementing these contractual requirements and being able to provide verification. The stakes are not just contract-eligibility, but operational continuity and national security.
Recommended reading

GSA CUI Compliance: What the New Procedural Guide Requires
10. Aero Turbine Inc. data leak
Date: July 2025
Impact: $1.75M False Claims Act Settlement related to unauthorized access to sensitive defense information and other cybersecurity violations
During a contract period with the Department of the Air Force, Aero Turbine and its private equity owner Gallant Capital Partners LLC allegedly failed to control the flow of, and limit unauthorized access to, sensitive defense information to a software company based in Egypt. In addition to this data leak, Aero Turbine allegedly failed to implement all cybersecurity controls in NIST 800-171, which increased its risk to significant exploitation of the system or exfiltration of sensitive defense information.
As a result of these and other cybersecurity violations, Aero Turbine and Gallant agreed to pay $1.75 million to resolve their liability under the False Claims Act on July 31, 2025.
Key learning
Unlike other examples of cyber attacks, a data leak usually happens when an internal party or source exposes sensitive data to an external party unintentionally or by accident. This was likely the case when the Gallant employee assisting Aero Turbine provided the foreign software company’s personnel in Egypt with CUI from Aero Turbine’s system.
However, because this failure (and other instances cited in the settlement) to comply with DoD contract specifications and cybersecurity requirements put DoD information and programs at risk of exploitation, it still resulted in an enforcement action and fine.
This sends a clear message to other organizations in the DIB that they must ensure they follow required cybersecurity standards to protect sensitive defense information, or face the consequences.
Recommended reading

$6.8 Billion in False Claims Act Recoveries: The DOJ’s Clear Warning to the Defense Industrial Base
11. WestJet cyber attack
Date: June 2025
Impact: Intermittent disruptions on website and mobile app
In June, Canadian airline WestJet disclosed a cybersecurity incident that disrupted access to its website and mobile app. While flights and operations were unaffected, internal systems were compromised, and customers encountered intermittent access issues. WestJet stated it was still investigating whether sensitive data had been accessed.
The FBI later warned that the attack could be linked to Scattered Spider, a threat group increasingly targeting the airline sector. The group uses social engineering tactics to trick IT help desks into granting access to internal systems, often by impersonating employees and bypassing MFA protections. Once inside, they exfiltrate sensitive data and may deploy ransomware as a secondary tactic.
Key learning
Organizations must adopt a multi-layered defense that includes regular security awareness training, especially around social engineering tactics. Educating employees, especially IT and support teams, on recognizing impersonation attempts can prevent attackers from gaining a foothold.
Recommended reading

The 13 Most Common Types of Social Engineering Attacks + How to Defend Against Them
12. Aflac social engineering attack
Date: June 2025
Impact: Exposure of sensitive customer, employee, and health data
On June 12, Aflac detected suspicious activity on its U.S. network. The insurance giant quickly initiated its cyber incident response plan, containing the breach within hours. The attacker (likely Scattered Spider) used social engineering techniques to gain unauthorized access and exfiltrated sensitive data including Social Security numbers, health info, and policy details.
This campaign was part of a larger series of coordinated attacks targeting the insurance industry. Although ransomware wasn’t deployed, the data theft alone had serious consequences for customer privacy and trust.
Key learning
Today, malicious insiders like Scattered Spider are able to move faster and cause more damage.
“If Scattered Spider is targeting your industry, get help immediately,” said Cynthia Kaiser, who until last month was deputy assistant director of the FBI’s Cyber Division and oversaw FBI teams investigating the hackers. “They can execute their full attacks in hours. Most other ransomware groups take days.”
This underscores the importance of organizations having robust cybersecurity monitoring in place to detect intrusions early before attackers can escalate privileges or deploy ransomware. Real-time threat detection and anomaly monitoring are essential for stopping fast-moving actors like Scattered Spider.
Recommended reading

Cybersecurity Monitoring: Explaining the What, Why & How
13. National Defense Corporation ransomware attack
Date: March 2025
Impact: 4.2TB of sensitive data breached
The Interlock Ransomware Group targeted National Defense Corporation (NDC) and its subsidiary AMTEC in a March cyberattack, exfiltrating 4.2 terabytes of data later leaked on the dark web. NDC, which manufactures lethal and non-lethal ammunition, reported the breach to the SEC, calling it a “system outage caused by a cybersecurity incident.”
The attack marked a shift in Interlock’s targeting strategy from broad, opportunistic campaigns to high-value defense contractors. Though classified data wasn’t directly exposed, procurement documents, logistics details, and supply chain information were compromised, creating long-term risk across the defense industrial base (DIB).
Key learning
Compliance frameworks like CMMC are critical for protecting sensitive, unclassified data, requiring defense contractors and subcontractors to implement robust access controls, encryption, and continuous monitoring, among other controls.
This incident emphasizes the importance of ensuring, even if you’re compliant yourself, that your entire supply chain, including third- and fourth-party vendors, meets similar security standards.
Recommended reading

CMMC 2.0 Compliance Guide: Requirements, Levels & Certification Costs
14. Microsoft zero-day vulnerability
Date: April 2025
Impact: Ransomware attacks via CLFS zero-day vulnerability on organizations across the globe
In April, Microsoft patched 126 vulnerabilities, including CVE-2025-29824, a zero-day flaw in the Windows Common Log File System (CLFS) exploited by the group Storm-2460. The attackers used a custom malware strain, PipeMagic, to escalate privileges and launch ransomware across multiple sectors worldwide.
While the entry point remains unclear, Microsoft confirmed the vulnerability allowed attackers with standard user access to gain elevated privileges, a key step in post-compromise ransomware deployment.
The CLFS vulnerability is part of a growing trend of privilege escalation flaws being actively exploited, according to Satnam Narang, senior staff research engineer at Tenable.
“Elevation of privilege flaws in CLFS have become especially popular among ransomware operators over the years,” Narang said. “While remote code execution flaws are consistently top overall Patch Tuesday figures, the data is reversed for zero-day exploitation. For the past two years, elevation of privilege flaws have led the pack and, so far in 2025, account for over half of all zero-days exploited.”
Key learning
With privilege escalation exploits now dominating zero-day attacks, organizations must implement a robust vulnerability management process that includes vulnerability scanning, patch management, and regular penetration testing to identify and fix vulnerabilities before attackers exploit them.
Recommended reading

Vulnerability Scanning Explained: What It Is & Why It’s Important for Compliance in 2025
15. Marks and Spencer Group attack
Date: April 2025
Impact: Data breach affecting 16.9 million customers and $27M in costs
U.K. retailer Marks & Spencer was one of several retailers impacted by a cyberattack linked to Scattered Spider The breach affected online shopping, inventory management, and exposed customer data, including payment details, though the company noted most payment data was masked.
The retail sector has become a hotbed for advanced persistent threat groups, with attackers disrupting operations and stealing data across multiple companies in coordinated campaigns.
Key learning
Considering that many of the most recent attacks in 2025 span multiple industries but are linked to the same group (Scattered Spider), this is a wakeup call for organizations across industries and the globe.
Having an incident response plan written down is essential, but only one step of the process. Actually testing it in a controlled environment through cybersecurity tabletop exercises is also a critical piece. Practicing realistic attack scenarios helps teams identify weak spots, refine response procedures, and reduce downtime during actual incidents.
Recommended reading

How to Run Effective Cybersecurity Tabletop Exercises + 6 Scenario Templates
Recent Cyber Attacks 2024
Cyberattacks in 2024 reflected an alarming expansion in both scale and tactics. From high-profile ransomware attacks to targeted phishing campaigns and third-party breaches, attackers focused on disrupting critical operations and exfiltrating sensitive data, often simultaneously.
Several common threads emerged:
- Credential abuse and phishing remained the top initial access methods
- Supply chain vulnerabilities were exploited to access broader ecosystems
- Regulatory pressure increased, with more organizations publicly disclosing incidents in SEC filings
- Attackers showed growing interest in infrastructure sectors like finance, energy, and logistics
These breaches serve as a critical reminder: even companies with mature cybersecurity programs aren’t immune. What matters most is how quickly and effectively they detect, respond, and recover.
16. LoanDepot ransomware attack
Date: January 2024
Impact: Data breach impacting 16.9M customers and $27M in response and recovery costs
In January, LoanDepot, a major mortgage lender, fell victim to a ransomware attack that exposed the sensitive data of approximately 16.9 million customers, including Social Security numbers, account numbers, names, addresses and other data.
The company took some systems offline in response to the cyberattack on January 8 and began restoring them on January 18. As a result of disrupted operations and other impacts of the cyber attack, LoanDepot incurred an estimated $27 million in response and recovery costs. This amount includes costs to investigate and remediate the cybersecurity incident, the costs of customer notifications and identity protection, professional fees including legal expenses, litigation settlement costs, and commission guarantees.
Key learning
This incident underscores the importance of having comprehensive security measures in place —including a strong cybersecurity remediation process — to safeguard sensitive customer information and minimize financial losses.
Having a robust cybersecurity remediation process that leverages automation and AI can help organizations proactively address vulnerabilities, minimize risks and potential damages if an incident does occur, and prevent similar attacks in the future. The remediation process should include identifying root causes, addressing weaknesses, and implementing lessons learned from incidents.
Recommended reading
Cybersecurity Remediation: A Guide to Protecting Your Business
17. Schneider Electric ransomware attack
Date: January 2024
Impact: 1.5TB Data Breach
In mid-January, the ransomware-as-a-service group Cactus infiltrated the networks of multinational energy management company Schneider Electric, reportedly stealing 1.5 terabytes of data from its Sustainability Business Division.
Since this division provides renewable energy and regulatory compliance consulting services to high-profile companies worldwide, including Allegiant Travel Company, Clorox, DHL, DuPont, Hilton, Lexmark, PepsiCo, and Walmart, a data breach of this magnitude would include mountains of sensitive information about these customers’ industrial control and automation systems and information about environmental and energy regulations compliance. Experts believed that customers were likely exerting significant pressure on the company to make a “record” ransomware payment to forestall the release of the sensitive data as a result.
In addition to the ransomware payment, a data breach like this is costly in other ways. It can damage the organization's reputation, erode customer trust, and lead to regulatory scrutiny.
Key learning
Schneider Electric confirmed another cyber attack in November 2024, its third ransomware attack reported in 18 months.
The ongoing attacks on Schneider Electric evince a finding from the IBM X-Force Threat Intelligence Index 2024: Manufacturing has been ranked as the top attacked industry for three years in a row, representing over a quarter (25.7%) of incidents within the top 10 attacked industries in 2024.
Because they are prime targets for cybercriminals due to their critical role in the economy and heavy reliance on connected devices and technologies, manufacturing companies must adopt a proactive cybersecurity strategy to address their sector's unique risks. This includes protecting operational technology (OT), adhering to evolving regulatory requirements, and ensuring business continuity amid increasing threats.
Recommended reading

Cybersecurity for manufacturing: Essential best practices and industry frameworks
18. Kawasaki Motors Europe cyber attack
Date: September 2024
Impact: Servers taken offline and 487GB of data stolen
Kawasaki Motors Europe experienced a significant cyber attack that forced the company to take servers offline to contain the breach. The attackers exfiltrated 487GB of data, which contained critical business documents, including financial information, banking records, dealership details, and internal communications. Later that month, Kawasaki Motors Europe was able to recover most of its servers and resume business with third-party suppliers and dealers. It also implemented enhanced monitoring operations and tightened access restrictions to prevent unauthorized access in the future.
Key learning
Organizations operating in the EU or entering the market must prioritize compliance with regulations like NIS2 to enhance cyber resilience. Failing to meet these standards can result in operational disruptions, reputational harm, and regulatory penalties.
Recommended reading

Understanding EU Cybersecurity: History, Regulations, and Certifications
19. Crowdstrike incident
Date: July 2024
Impact: Global IT outage estimated to cost $1B
In July 2024, a global outage linked to CrowdStrike caused significant disruptions across various industries. The incident, which was caused by a flawed update to a cloud-based security software of CrowdStrike that affected 8.5 million Microsoft Windows devices, led to widespread disruptions of airlines, banks, broadcasters, healthcare providers, retail payment terminals, and cash machines globally. Airlines cancelled thousands of flights, supermarkets couldn’t accept credit card payments, and hospitals cancelled non-urgent surgeries, among other examples.
In total, the cost of the outage is estimated to be over $1 billion.
Key learning
This incident highlighted the risks of relying on a single IT service provider without robust incident response mechanisms in place.
Organizations need a resilient cyber incident response plan to reduce downtime and financial losses if a similar incident occurs. Such plans should include clear communication strategies, rapid containment protocols, and regular testing to ensure you can maintain the resilience of your business and services in the face of a cyber attack or cyber failure.
Recommended reading

How to Build a Resilient Cyber Incident Response Plan: Challenges & Best Practices
20. Salt Typhoon cyber attack
Date: September 2024
Impact: Data breach of DoD’s unclassified communications from multiple telecommunications companies
The Salt Typhoon cyber attack, attributed to Chinese threat actors, targeted at least eight US telecommunications companies in pursuit of sensitive information, including unclassified voice, video, and text communications of the Department of Defense (DoD).
The US believes that the hackers were able to gain access to communications of senior U.S. government officials and prominent political figures through the hack, as reported by Fast Company.
Key learning
This attack, considered the worst telecom attack in the country’s history, emphasizes the importance of safeguarding sensitive government information against nation-state actors, especially in the defense supply chain.
While advisors have called for new mandatory cybersecurity requirements for the telecom sector, including rules on secure configurations and network monitoring, CMMC 2.0 was created to help address concerns about the safety of critical national infrastructure and important information related to national security. Organizations bidding on DoD contracts or handling DoD information must comply with CMMC requirements. Achieving the appropriate CMMC level ensures baseline security and protects against advanced threats.
Recommended reading

CMMC Hub: 30+ Free Resources to Simplify Certification
Recent Cyber Attacks 2023
In 2023, the cybersecurity landscape was defined by disruption at scale. Threat actors launched attacks that shut down production lines, compromised cloud environments, and affected tens of millions of consumers globally. The year’s biggest incidents weren’t just about data loss. They had serious implications for public safety, national security, and economic stability.
Key themes across 2023 breaches included:
- The rise of data extortion without deploying ransomware
- Attacks on managed service providers to gain downstream access
- Growing interest in healthcare and critical infrastructure
- Continued exploitation of known but unpatched vulnerabilities
Looking back at these events provides valuable insight into threat actor behavior and the defense strategies that proved (in)effective under pressure. Each example is a case study in how lapses in patching, access control, or third-party oversight can have ripple effects across entire industries.
21. ICBC Financial Services ransomware attack
Date: November 2023
Impact: Disruption of the US Treasury market
In November, a subsidiary of the Industrial and Commercial Bank of China (ICBC), the ICBC Financial Services, experienced a ransomware attack that disrupted some operating systems, including those used to clear US Treasury trades and repo financing. As a result of this disruption, the brokerage was unable to settle trades for other market players and temporarily owed BNY Mellon $9 billion.
This not only highlights the growing payment interruption risk that financial institutions face due to cybersecurity incidents — it also reflects the increasing scale of such incidents. Because financial systems and business operations are increasingly interconnected, the impact of a cyber attack is rarely limited to the target organization. Instead, it has a ripple effect that can affect organizations and economies across the world.
The attack on ICBC Financial Services, for example, disrupted the US Treasury market, which plays a crucial role in global finance.
Key learning
Cyber attacks like this are expected to increase as threat actors continue to target important financial institutions and infrastructure in major economies. If successful, an attack on one organization can impact partners, suppliers, and customers across the globe.
This emphasizes the importance of supply chain risk management. Supply chain risk management involves identifying and assessing threats throughout the supply chain and developing mitigation strategies to protect the integrity, trustworthiness, and authenticity of products and services within that chain. Having a defined process in place can help your organization minimize the likelihood and magnitude of these risks to the supply chain.
Recommended reading

Supply Chain Risk Management: A Breakdown of the Process + Policy Template
22. MGM Resorts phishing attack
Date: September 2023
Impact: Over $100 million in financial losses
After detecting a cyber attack that disrupted its operations in late September 2023, MGM Resorts International shut down its systems to contain the damage. It then reported that it would take a $100 million hit to its third-quarter results, as it worked to restore its systems. The casino giant also expected to incur a one-time cost of approximately $10 million related to the attack.
It appears that the hackers used a social engineering technique known as vishing. After finding an employee’s information on LinkedIn, the hackers impersonated the employee in a call to MGM’s IT help desk to obtain credentials to access and infect the systems.
Key learning
Social engineering attacks are expected to increase in sophistication and frequency due to AI, which enables threat actors to create more convincing and legitimate sounding phishing emails, deepfakes, vishing calls, and more.
Organizations that extensively use AI and automation to enhance their cybersecurity capabilities will be best positioned to defend against this weaponized use of AI by cybercriminals. In a study by Capgemini Research Institute, 69% of executives said that AI is necessary to effectively respond to cyberattacks and results in higher efficiency for cybersecurity analysts.
Recommended reading

AI in Cybersecurity: How It’s Used + 8 Latest Developments
23. Boeing ransomware attack
Date: October 2023
Impact: 43GB data leak
In October 2023, Boeing, one of the world's largest defense and space contractors, suffered a cyber attack that impacted its parts and distribution business. This attack was traced to a vulnerability in Citrix’s software, known as Citrix Bleed, that was exploited by the ransomware group LockBit 3.0. LockBit later leaked more than 43 gigabytes of data allegedly stolen from Boeing’s system when the aerospace company refused to pay the demanded ransom.
Exploitation of CitrixBleed impacted other major organizations as well, including the U.S. branch of ICBC and logistics firm DP World. The majority of affected systems were reported to be located in North America. It’s estimated that US organizations hit by LockBit paid as much as $90 million in ransom between 2020 and mid-2023.
As a result of the incident at Boeing, the Cybersecurity and Infrastructure Security Agency (CISA), the FBI, and Australian Cyber Security Center issued a cybersecurity advisory urging organizations to patch against the actively exploited flaw immediately if they haven’t done so already.
Key learning
In October, Citrix posted a security bulletin rating the bug a 9.4 out of 10 on the CVSS severity scale. However, in November, thousands of instances where the tool was used were still vulnerable to the issue, including nearly 2,000 in North America alone. There was widespread exploitation of the Citrix vulnerability in unpatched software services throughout both private and public networks as a result.
Managing exposure to discovered vulnerabilities is a key aspect of vulnerability management, alongside discovering, categorizing, and prioritizing vulnerabilities and analyzing the root cause of vulnerabilities. Having a robust vulnerability management program can help an organization develop a comprehensive understanding of its risk profile, understand what controls need to be implemented for risk mitigation, and prevent repeat vulnerabilities.
Recommended reading

A Step-by-Step Guide to the Vulnerability Management Process [+ Policy Template]
24. The British Library ransomware attack
Date: October 2023
Impact: Major disruptions to systems and operations and 600GB data leak
The UK's largest library was hit by a cyber attack on the last weekend of October. While the British Library took immediate action to isolate and protect its network, its online systems and services were massively disrupted, its website went down, and it initially lost access to even basic communication tools such as email.
On January 15, it began a phased return of certain key services, starting with the restoration of a reference-only version of its main catalog. However, the disruption to some of its operations is expected to persist for months, possibly until next fall or even longer.
In total, the cost of recovering the British Library’s IT systems is estimated to be as high as £7 million, which represents about 40% of its unallocated cash reserves.
Key learning
To help prevent lengthy and costly recoveries in the event of a successful ransomware attack, organizations must update their cyber resiliency measures, including putting a disaster recovery plan in place.
Having a disaster recovery plan in place that is well-designed and regularly maintained can help organizations minimize downtime, reduce financial losses, protect critical data, and provide peace of mind for employees.
Recommended reading

How to Write a Disaster Recovery Plan + Template
25. TruePill data breach
Date: August 2023
Impact: Data breach impacting 2.3M patients
Truepill experienced a data breach in late August, which exposed the personal data of more than 2.3 million patients. Postmeds, the parent company behind TruePill, published a data breach notice that explained that the attackers accessed files containing sensitive patient data, including names, unspecified demographic information, medication type, and the name of the patient’s prescribing physician.
While the company did not say how its systems were compromised or what specific measures it implemented to prevent future breaches, a class action lawsuit alleges that the cybersecurity incident was the result of inadequate data security measures — including the failure to encrypt sensitive healthcare information stored on its servers.
Key learning
Healthcare is one of the most targeted industries by threat actors. In 2022, 89% of the healthcare organizations experienced an average of 43 attacks in the past 12 months, which equates to almost one attack per week. The healthcare industry was also the most common victim of third-party breaches in 2022, accounting for almost 35% of all incidents.
While third-party security is critical across industries, it’s particularly important in the healthcare industry due to its susceptibility to cyber attacks. Conducting third-party risk assessments, tracking metrics and KPIs like pass rate for security questionnaires, and using automation can help strengthen a healthcare organization’s third-party risk management program and protect it from data breaches like this one.
Recommended reading

Third-Party Security: 8 Steps To Assessing Risks And Protecting Your Ecosystem
26. 23andMe hack
Date: October 2023
Impact: Data breach impacting 6.9 million users
23andMe disclosed that hackers accessed about 14,000 accounts in a cybersecurity incident in October. The scope ended up being much larger due to 23andMe’s DNA Relatives feature, which matches users with their relatives. By accessing those 14,000 accounts, hackers were also able to access the profile information of millions of other users. In total, the data breach is known to affect roughly half of 23andMe’s total reported 14 million customers.
When disclosing the incident in October, 23andMe said the data breach was caused by customers reusing passwords. Hackers were able to use publicly known passwords released in other companies’ data breaches to brute-force the victims’ accounts.
Key learning
While the 23andMe breach showed the impact that poor password hygiene can have on data security, it also highlighted the need for organizations to take responsibility for protecting user data.
Maintaining a strong incident response plan is one security tactic that organizations can implement. For example, following the data security incident, 23andMe required all users to reset their passwords and now requires all new and existing users to use two-step verification when logging in to the website.
Recommended reading

How to Create an Incident Response Plan + Template
27. Mr. Cooper ransomware attack
Date: October 2023
Impact: Data breach impacting 14.7M customers and $25Min response and recovery costs
After reviewing a cyberattack that took place in October 2023, Mr. Cooper determined that personal data on every current and former customer of Mr. Cooper Group was stolen, which amounted to more than 14 million people.
Mr. Cooper shut down multiple systems after it discovered the cyberattack, which prevented millions of customers from making payments and processing mortgage transactions. The company set up alternative payment methods for customers after the attack, including by phone, mail service, Western Union and MoneyGram..
The mortgage and loan giant expected vendor expenses related to its response, recovery, and identity protection services to reach $25 million in the fourth quarter.
Key learning
Mr. Cooper is just one of many financial services firms that was hit by a suspected ransomware attack in 2023. Other notable examples include LoanDepot, Fidelity National Financial, and First American Financial.
Since these cyberattacks undermine the security and confidence in national and international financial systems and endanger financial stability, regulatory expectations for all financial services institutions have increased. More regulation has passed, expanded, or been increasingly enforced to ensure these institutions have a comprehensive information security program in place, including the FTC Safeguards Rule and New York Department of Financial Services (NYDFS) NYCRR 500.
Meeting these regulatory requirements can not only help avoid penalties and fines — it can also help protect the security and confidentiality of customer information held by financial institutions.
Recommended reading
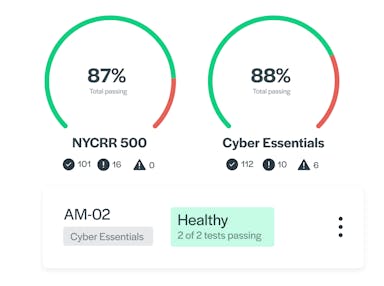
Secureframe Adds New Frameworks to Help Financial Institutions Achieve and Maintain Cybersecurity Compliance
28. Dollar Tree third-party breach
Date: August 2023
Impact: Data breach impacting 2M people
In August 2023, Dollar Tree was impacted by a third-party data breach affecting approximately 1.98 million people. One of its vendors, Zeroed-In Technologies, LLC, suffered a security incident in which threat actors stole the information of Dollar Tree and Family Dollar employees and customers, including names, dates of birth, and Social Security numbers (SSNs).
Allegedly, Dollar Tree shared the private, unencrypted information of its employees and customers with Zeroed-In, which stored that information in an unencrypted, Internet-accessible environment on its public network. An unauthorized party then gained access to the company’s systems.
Key learning
Many organizations work with outside vendors to cut down on costs or better serve customers, which requires them to share access to sensitive information with third parties. That means organizations must put the same amount of scrutiny on the risk management practices of outside vendors as they do their own.
A vendor risk management program provides companies with visibility into who they work with, how they work with them, what security controls each vendor has implemented, and their security posture over time, which can help them identify potential threats before they impact their business.
Recommended reading
Vendor Risk Management (VRM): How to Implement a VRM Program that Prevents Third-Party Breaches
29. DP World Australia cyber attack
Date: November 2023
Impact: Major disruptions to operations that led to 30K shipping container backlog
DP World Australia is one of the country's largest ports operators and manages approximately 40% of Australia’s total flow of goods. In November 2023, it experienced a cyber attack that crippled its operations at container terminals in Melbourne, Sydney, Brisbane, and Fremantle.
Once it detected unauthorized access to the company’s Australian corporate network, DP World Australia disconnected the network from the Internet in order to contain the incident. This shut down port operations across Australia for three days, prompting a backup of some 30,000 shipping containers.
Key learning
The DP World cyber attack represents one of the latest large-scale criminal attacks on critical infrastructure and has prompted demand for governments to prioritize and invest in cybersecurity measures, especially for critical infrastructures like ports. The demand is especially high in Australia, since attacks against the country’s critical infrastructure, businesses and homes have surged recently, with one attack happening every six minutes according to the Australian Cyber Security Centre.
Cybersecurity measures can help protect the availability and resilience of critical infrastructure and the essential services it provides.
Recommended reading

Cybersecurity Explained: What It Is & 12 Reasons Cybersecurity is Important
30. Ardent Health Services ransomware attack
Date: November 2023
Impact: Critical care impacted in at least three states
Ardent Health Services owns and operates 30 hospitals and more than 200 sites of care with more than 1,300 aligned providers in six states. When it was hit by a ransomware attack in November 2023, the company proactively took its network offline, suspending all user access to its information technology applications.
This resulted in disruptions to operations in facilities across multiple states. Some had to reschedule non-emergent, elective procedures and divert emergency room patients to other area hospitals until systems were back online. Patients also reported being unable to refill prescriptions and make appointments online, and having their procedures rescheduled or postponed.
Key learning
According to a report by the FBI’s Internet Crime Complaint Center (IC3), the FBI received 870 reports of ransomware attacks aimed at organizations belonging to 16 critical infrastructure sectors and the healthcare sector topped the list with 210 reports of ransomware attacks.
Increasingly sophisticated and malicious cyber campaigns targeting critical infrastructure like the example above threaten the public and private sector as well as the American people’s security and privacy. In response, the US government has created several information security standards and frameworks for reducing risk and improving data security.
Federal contractors and government agencies typically comply with these federal standards and frameworks, but any organization can benefit from implementing these stringent and comprehensive requirements. Doing so will have important ramifications for the public sector, the private sector, and ultimately national security and privacy.
Recommended reading

What 2025 Healthcare Data Breaches & Biggest of All Time Reveal About Protecting PHI
Cyber attack trends
Cyberattacks are constantly evolving, and so must your defenses. Looking across major breaches over the past two years, we’ve pulled out high-level trends to help you better understand the latest threat landscape.
These aren’t just headlines. They’re signals that attackers are adapting faster, targeting more strategically, and taking advantage of emerging technologies and global instability. Understanding these trends is essential for strengthening your defenses and aligning with security frameworks that address modern risks.

1. AI-generated attacks are scaling threats at unprecedented speed
AI not only lowers the bar for entry into cyber crime, it also enhances attacker capability by improving the scale, speed, and effectiveness of existing attack methods.
Patrick Smyth, Principal Developer Relations Engineer at Chainguard, points to the decrease in time to exploit, the time from when a vulnerability is publicized until an exploit for that vulnerability has been discovered in the wild, as a practical measure of how AI has dramatically enhanced real-world attacker capability. On average, time to exploit was over 700 days in 2020. It dropped down to only 44 days in 2025.
As a result of the speed that AI offers, cyber attacks by AI-enabled adversaries are increasing rapidly, with CrowdStrike’s 2026 Global Threat Report reporting an 89% YoY increase.
Experts at the Center for Strategic and International Studies emphasize that this is the biggest threat today: not fully autonomous AI cyber attacks, but how AI vastly reduces the cost, time, and skill required to mount effective attacks using pre-existing methods. For example, research from Google’s M-Trends 2026 report found that attackers are shifting away from mass email campaigns to hyper-personalized, rapport-building social engineering thanks to large language models (LLMs) acting as a strategic force multiplier.
Rapid patching, sophisticated identity controls, and defense-in-depth are all operational necessities to counter AI-enabled adversaries that work much faster and stealthily.
2. Cyber attacks are increasingly complex, coordinated, and disruptive
Cyber operations are becoming more "industrialized," with initial access brokers, ransomware operators, and data exfiltration specialists working in tandem, each playing a specialized role to maximize damage. And they're coordinating faster than ever.
According to the M-Trends 2026 report, the median time between an initial access event and hand-off to a secondary threat group dropped from more than 8 hours in 2022 to just 22 seconds in 2025. That's not an incremental improvement in attacker efficiency. It's a huge leap forward.Defenders who once had hours to detect and contain an intrusion before it escalated now have almost none.
The targets are also shifting. Attacks increasingly focus on governments, critical infrastructure, and multinational corporations, often involving cross-border collaboration between cybercriminal groups, hacktivists, and state-sponsored actors. The convergence of financial crime, espionage, and geopolitical disruption into single campaigns makes these threats harder to attribute, harder to anticipate, and harder to recover from.
3. Cyber attacks increasingly driven by disruption and espionage, not just financial gain
Financial motivation is no longer the defining force behind cyber attacks. In 2020, 38% of incidents were financially driven. In 2025, that figure had dropped to 30%, according to M-Trends 2026.
Increasingly, attacks are designed to gather intelligence, disrupt critical services, influence political outcomes, or establish long-term footholds in strategic networks, not to extract an immediate payout. This shift is visible in the rise of APT activity targeting governments, defense supply chains, and critical infrastructure, where the primary objective is persistence and leverage rather than ransom.
This doesn't mean financially motivated crime is declining in scale. It isn't, as we’ll explain below. But it does mean defenders can no longer assume that disruption or data theft is always a precursor to a ransom demand. Sometimes disruption is the goal.
4. Cybercrime losses are hitting record highs
Even as a growing share of attacks are motivated by espionage or disruption rather than direct financial gain, the economic toll of cybercrime continues to climb. According to the FBI's 2025 Internet Crime Report, US cybercrime losses hit a historical high of nearly $21 billion, a 26% year-over-year increase. In the EU, cyber-enabled fraud alone cost $64.1 billion in 2025, according to Europol's IOCTA 2026.
These record highs aren’t contradictory to the diversification of attack motives; they reflect two parallel realities:
- Financially motivated crime (fraud, ransomware, business email compromise) continues to scale in volume and sophistication, largely due to AI.
- Attacks motivated by disruption or espionage carry their own massive economic costs: operational downtime, recovery expenses, legal liability, and lost contracts.
The Stryker attack in early 2026 is a clear example. While the attacker's motivation may not have been a ransom payout, the financial impact of the attack was material enough to affect quarterly earnings and trigger lawsuits. The record losses are a reminder that the cost of recovering from a cyber attack extends well beyond any ransom paid.
5. Supply chain attacks are targeting trusted tooling
Attackers have learned that breaching a well-defended organization directly is harder than compromising something that organization already trusts. By targeting software distributors, managed service providers, and widely-used developer tools, a single successful attack can cascade to thousands of downstream victims, without ever touching their perimeters directly.
The scale of this shift is significant. According to IBM's 2026 X-Force Threat Intelligence Index, large supply chain and third-party compromises have nearly quadrupled since 2020. And the targets are getting more strategic: from compromised developer tools to exposed AI libraries, threat actors are increasingly pursuing what researchers call "ecosystem-level targeting,” compromising a single trusted component to gain indirect access to high-value targets at scale and often impact millions of users with a single breach.
What makes these attacks particularly difficult to detect is that once inside, adversaries move laterally using legitimate credentials and processes. Nothing looks obviously wrong. The Trivy supply chain attack in March 2026 illustrated this precisely: a widely-used vulnerability scanner was compromised for roughly 12 hours, silently harvesting CI/CD secrets from pipelines that appeared to be running normally.
For ransomware groups in particular, this one-to-many attack vector is expected to remain a top priority through 2026 and beyond. Defenders need to treat their software supply chain with the same scrutiny they apply to their own systems.
6. Ransomware is evolving and still the top threat
According to Recorded Future Intelligence, publicly reported ransomware attacks increased 47% year-over-year.
Already one of the biggest global threats, ransomware is expected to continue to increase due to advancements in AI and threat actors employing increasingly sophisticated techniques, including multi-extortion tactics and supply chain compromises. Ransomware groups are no longer just encrypting data, they are actively targeting backup infrastructure, identity services, and virtualization management planes in order to ensure organizations can’t restore the data instead of paying the ransom. They’re also increasingly exfiltrating data rather than encrypting it, and then threatening to publicly release it unless ransom demands are met.
Ransomware-as-a-service platforms also continue to democratize access to ransomware tools, enabling even more cybercriminals (especially low-skilled affiliates or disgruntled insiders) to participate in extortion schemes and launch their own attacks.
However, with ransomware groups reportedly making less money despite a significant increase in attacks, some groups are shifting away from mobilizing affiliates through RaaS and instead focusing on recruiting corporate insiders or gig workers to steal data.
7. Zero-day exploitation stabilizing, prioritizing edge devices
Zero-day vulnerabilities, flaws that are exploited before vendors release patches, are now central to many high-profile attacks. Threat actors are weaponizing zero-days not just for access, but also for privilege escalation, lateral movement, and data exfiltration.
While the volume of zero-days in 2025 (90) is lower than the record high observed in 2023 (100), Google Threat Intelligence Group (GTIG) continued to observe that enterprise software and edge devices remain prime targets. Marking a new high, 48% of 2025’s zero-days targeted enterprise-grade technology, which consists of highly interconnected platforms that provide privileged access across networks and data assets.
State-sponsored espionage groups continue to prioritize edge devices and security appliances as prime entry points into victim networks, with just over half of attributed zero-day exploitation by these groups focused on these technologies.
8. Time between disclosure and exploitation is shrinking fast
One of the most alarming trends is how little time defenders now have. According to CISA’s Known Exploited Vulnerabilities (KEV) data, over 25% of vulnerabilities exploited in Q1 2025 were attacked within 24 hours of being disclosed.
This trend, sometimes called “patch gap exploitation,” puts intense pressure on IT and security teams to move quickly from detection to remediation, often with incomplete context or limited resources. Automation and prioritization are now essential for effective vulnerability management.
9. CVE volumes are overwhelming defenders
The number of known vulnerabilities continues to explode. From 2020 to 2025, CVE submissions increased 263%. In 2024, over 40,000 CVEs were disclosed, and 2025 reached nearly 50,000. The volume alone makes it difficult to identify which issues to patch first, especially as attacker playbooks grow more dynamic.
Vulnerability exploitation was linked to 20% of breaches in the 2025 Verizon Data Breach Investigations Report (DBIR), putting it on par with stolen credentials and ahead of phishing as a breach vector. This means defenders must focus not only on quantity but on prioritizing what matters most, with the help of tools like CVSS scoring, threat intelligence, and AI-based vulnerability triage.
Recommended reading

210+ Cybersecurity Statistics to Inspire Action This Year [Updated Q4 2025]
How to prevent cybersecurity attacks
Cybersecurity attacks aren’t just increasing in number. They’re evolving in speed, complexity, and impact.
While no defense is foolproof, there are proven strategies that can dramatically reduce your organization’s risk exposure and ability to recover from an attack.
The tips below combine technical, procedural, and organizational best practices to help mitigate the likelihood and impact of a successful cyberattack. Many of these are also foundational requirements in security frameworks like SOC 2, NIST 800-53, CMMC, and ISO 27001, making them not only smart security decisions but essential steps for compliance.
1. Provide security awareness training to employees
A comprehensive training program can help employees understand common cyber threats such as phishing attacks, social engineering tactics, and malware, identify suspicious emails, links, and attachments, and understand the importance of following best practices and reporting any security incidents promptly.
Having a program in place that trains employees as they onboard and on a recurring basis about cybersecurity best practices, common threats, and their roles and responsibilities in safeguarding sensitive information can help your organization reduce the risk of human error leading to cyber attacks and breaches. It can also help you meet security and privacy compliance requirements for SOC 2®, HIPAA, PCI DSS, GDPR, and other frameworks.
2. Implement security controls to reduce your risk exposure
You can reduce your organization’s exposure to some types of cyber attack on systems that are exposed to the Internet by implementing security controls like:
- Malware defenses
- Boundary firewalls and internet gateways
- Password policy
- User access controls
- Patch management
3. Comply with cybersecurity standards and regulations
Cybersecurity frameworks require organizations to implement robust security measures, establishing a baseline of protection against cyber threats. By adhering to these standards, organizations must conduct regular risk assessments, identify vulnerabilities and potential attack vectors, and implement technical and administrative safeguards. These controls bolster defenses and mitigate the likelihood and impact of cyber attacks.
4. Continuously monitor for threats and misconfigurations
Attackers move fast, sometimes within hours of gaining access, so real-time detection is critical. Continuous monitoring helps you spot suspicious behavior, unauthorized changes, or misconfigured systems before they’re exploited. Continuous monitoring also supports compliance and audit readiness by maintaining visibility into your control environment.
5. Evaluate and manage third-party risks
Vendors, contractors, and other third parties can introduce serious vulnerabilities into your environment. Many recent breaches began not with a direct attack on the victim organization, but through a trusted partner or service provider.
Establish a formal third-party risk management (TPRM) process. Assess the security posture of your vendors, ensure they meet your security requirements, and monitor their compliance over time. Include third-party security in your incident response and business continuity planning.
6. Implement Secure-by-Design principles
Patching and scanning are still necessary, but they can no longer keep pace with today’s exploitation speed and scale. To stay ahead of attackers, organizations must rethink how systems are built in the first place.
CISA and its international partners are calling on every technology provider to take ownership at the executive level to ensure their products are “secure by design.” Secure by design means embedding security into every stage of system development and procurement, not just bolting it on after deployment. This includes minimizing the attack surface, eliminating default credentials, disabling unnecessary features, and enforcing strong authentication by default.
Reducing the exploitability of software and infrastructure upfront is key to long-term security resilience.
Recommended reading
Secure by Design: What Does It Mean & How to Reasonably Implement It
How Secureframe can help bolster your cybersecurity posture
Organizations today are challenged with mitigating increasingly complex risks and threats and continuing to comply with an increasing depth and breadth of regulation.
Secureframe can help by simplifying and automating manual tasks related to security, privacy, and compliance. With Secureframe, you can:
- Consolidate compliance and risk data in one source of truth via 300+ native integrations and the Secureframe API.
- Automate cloud remediation, risk assessments, policy management, and security questionnaires with AI.
- Closely monitor and manage your third-party vendor relationships.
- Conduct continuous monitoring to look for gaps in controls to maintain continuous compliance
- Automate the assigning, tracking, and reporting of required security and privacy compliance training.
- Get personalized advice based on your company’s unique risks and industry requirements from our in-house compliance team.
To learn more about how Secureframe can play an integral part in enhancing your security and compliance posture, request a demo today.
Get industry insights, news & more in your inbox
Secureframe Insights is our monthly newsletter covering the latest cybersecurity and compliance news, insights, and events — from changing regulations to compliance checklists and more.
Join thousands of subscribers in getting these expert insights delivered straight to your inbox.

FAQs
What is the most famous cyber attack?
One of the most famous recent cyber attacks is the NotPetya attack, which began in 2017, when Russian military hackers launched a malware attack targeting Ukraine that rapidly spread to more than 60 countries and destroyed the systems of thousands of multinational companies, including the global transport and logistics giant Maersk, the pharmaceutical giant Merck, FedEx’s European subsidiary TNT Express, French construction company Saint-Gobain, food producer Mondelēz, and manufacturer Reckitt Benckiser, among others. With the total damage estimated at more than $10 billion, NotPetya is still considered the most destructive and costly cyberattack in history.
What was the largest data breach in 2023?
More than 3.6 billion records were exposed when DarkBeam, a digital protection firm, left an Elasticsearch and Kibana interface unprotected. These records contained user emails and passwords from previously reported and non-reported data breaches.
What was the massive ransomware attack in 2023?
CL0P Ransomware Gang, also known as TA505, began launching a widespread attack in May 2023 after exploiting a previously unknown SQL injection vulnerability in Progress Software's MOVEit Transfer. This attack targeted thousands of government, public, and business organizations all over the world, with the vast majority being US-based entities.
What is the most recent cyber attack?
The most recent cyber attack as of writing this article is the ongoing attack on Instructure, which was disclosed on April 30 and caused Canvas to go offline on May 7, affecting approximately 9,000 schools and universities. While the system was back online that day, the ransomware group ShinyHunters claimed responsibility for the breach and alleged they stole 3.65 terabytes of data belonging to 275 million students, teachers, and other individuals. Ongoing analysis is underway to determine the full scope and potential fallout.
What websites show recent cyber security attacks?
To stay updated on real-time cyber threats, incidents, and breaches, consider these reputable sources:
- The Hacker News: Leading cybersecurity news site with threat intelligence, breach updates, and expert analysis
- Dark Reading (Cyberattacks & Data Breaches): Covers data breaches, advanced threats, and operational cybersecurity news
- CSIS Significant Cyber Incidents Timeline: A timeline listing major global cyber incidents, especially state-level or high-impact breaches

Anna Fitzgerald
Senior Content Marketing Manager
Anna Fitzgerald is a digital and product marketing professional with nearly a decade of experience delivering high-quality content across highly regulated and technical industries, including healthcare, web development, and cybersecurity compliance. At Secureframe, she specializes in translating complex regulatory frameworks—such as CMMC, FedRAMP, NIST, and SOC 2—into practical resources that help organizations of all sizes and maturity levels meet evolving compliance requirements and improve their overall risk management strategy.

Rob Gutierrez
Senior Cybersecurity and Compliance Manager, CISA, CCSK, CMMC RP
Rob Gutierrez is an information security leader with nearly a decade of experience in GRC, IT audit, cybersecurity, FedRAMP, cloud, and supply chain assessments. As a former auditor and security consultant, Rob performed and managed CMMC, FedRAMP, FISMA, and other security and regulatory audits. At Secureframe, he’s helped hundreds of customers achieve compliance with federal and commercial frameworks, including NIST 800-171, NIST 800-53, FedRAMP, CMMC, SOC 2, and ISO 27001.