Interview with an ISO 27001 Auditor: How Do You Maintain Certification?
Emily Bonnie
Senior Content Marketing Manager
Cavan Leung
Senior Compliance Manager
Information is the currency of the modern world.
Sadly, many organizations lack the proper controls and standards to protect their information assets.
This is especially dangerous for companies that deal with confidential user data. A data breach can be a painful hit — one many organizations won’t recover from.
ISO 27001 helps you implement a solid information security management system (ISMS) to protect your most valuable information assets and mitigate security risks.
We interviewed Mahtab Haider, the director of ISO Service Line at The Cadence Group, and asked him seven questions about maintaining your ISO 27001 certification.
Before we dive into the actual interview questions, let’s start with a quick recap of the ISO 27001 standard.
What is ISO 27001?
ISO 27001 is an international standard that explores an organization’s security controls and processes to ensure they protect users’ confidential information.
To do this, ISO 27001 analyzes an organization’s security performance in three main areas:
- Confidentiality: How are you protecting confidential user information against unauthorized access?
- Integrity: What are you doing to ensure your data is accurate and complete?
- Availability: What processes do you have in place to make your information available to users when they need it?
ISO 27001 provides you with the guidelines and requirements you need to implement an information security management system (ISMS) the right way.
An organization’s ISMS represents the collection of all security controls in your business. That is, everything you’re doing to manage and coordinate your internal security controls, including:
- People: Every member of your organization (i.e., employees, stakeholders, consultants, and leaders)
- Processes and operations: Processes and operations that are directly or indirectly related to protecting confidential information
- Systems, software, and technology: Computer systems, SaaS providers, apps, and any other technology that helps you implement your security controls
- Risks and threats involved: Contingency plans and controls you use to mitigate risks and avoid threats
- Policies and regulations: Policies and regulations to ensure organization-wide compliance
Now that we've covered the basics of ISO 27001, let’s dive into the interview questions.
1. How long does an ISO 27001 certification last?
Haider explains: “ISO 27001 certification lasts three years. The first year comprises a full certification audit while the second and third years are surveillance audits.”
What does this mean?
Once an auditor reviews your controls and issues your certification, you’re compliant for three years. But, it doesn’t mean you shouldn’t do anything to maintain that certification.
Here’s how it goes:
- First-year: The auditor performs a full analysis of your organization’s controls against ISO 27001 standards, including documentation review, field review, findings analysis, security audit reporting, and management review.
- Second and third-year: The auditor reviews that your controls are still performing and suggests updates when needed.
If one of your controls fails while your certificate is still valid, you’re obligated to document the incident, inform relevant stakeholders, and fix the issue. Otherwise, you can lose your certification.
In other words, getting your ISO 27001 certification is just the first step of an ongoing process.
2. What should a company do to maintain its ISMS after receiving ISO 27001 certification?
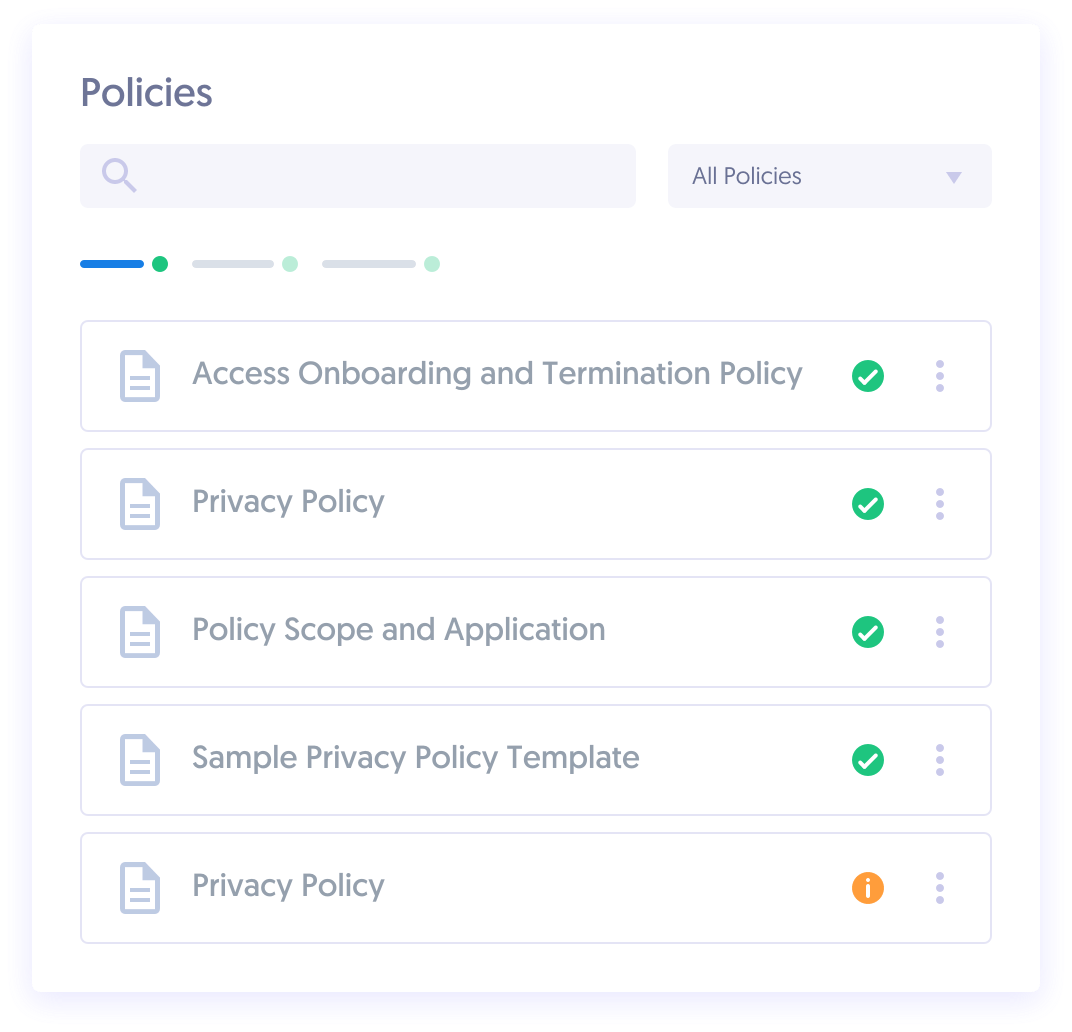
“Continued review and updates to its information security policies and procedures along with process and control implementation are needed to maintain ISMS,” says Haider.
The ISO 27001 standard suggests implementing an internal auditing program. This way, you can spot potential problems and fix them before they start snowballing into bigger issues that can threaten your certification.
You should designate an internal auditor that will be responsible for evaluating your controls periodically.
At this stage, performance analysis can help you understand how your controls are working and improve your actions accordingly.
We suggest you also perform periodic gap analyses to determine whether your controls are still meeting ISO 27001 requirements.
On top of that, define a specific calendar for internal audits and schedule meetings to document and review your findings.
3. What are some common mistakes you see teams making as a result of letting their guard down after the audit?
According to Haider, “Organizational changes are inevitable. Once certified, companies must maintain in-house knowledge of ISMS documentation and processes. It’s a common pitfall for organizations to lose sight of control compliance and policy effectiveness while going through people processes and organizational changes.”
This is especially relevant for large organizations dealing with multiple departments. Siloed, cross-departmental information can open you up to vulnerabilities. Why? Lack of control over your change management processes can lead to poor communication and potential security issues.
We suggest you adopt a project management solution that helps you centralize your information into a single source of truth. This way, you can improve organization-wide transparency, remove silos between departments, and ensure ISMS adoption.
4. I’ve received an ISO 27001 certificate, but a new threat to information security emerges. Do I need to update my documentation?
According to Haider, yes. “Information security risk assessment is another venue where information security threats can be registered and monitored for appropriate mitigation actions.”
If you discover a new threat that can jeopardize your information security, you must update your documentation describing the threat and the potential contingency plans and actions you can take to mitigate risk.
ISO 27001 Clause 6 states that organizations must analyze and consider any potential risk and threat involved with any security control.
You should also document a clear schedule of action to deal with risks in case they materialize.
5. If a company suffers a data breach after getting ISO 27001 certified, can they lose their certificate?
“Incident management domain requirements of ISO 27001 certification standard require organizations to document and inform stakeholders of any security incidents that take place during the certification period. If they do not follow the incident management plan/policy during a surveillance audit, this could be categorized as major non-conformity, which will lead to the discontinuation of ISO certification,” says Haider.
This is why you should constantly be monitoring the performance of your controls.
Cyber-attacks have skyrocketed since the pandemic hit. The FBI reports a 300% increase in cybercrime over the past year alone. Cybersecurity is expected to cost businesses approximately $6 trillion globally by the end of this year.
Many organizations ignore the importance of monitoring and evaluating security controls after getting ISO certification. The problem is that a data breach can often cost you more than a certification. It can tank your entire business.
6. How do you reapply for ISO 27001 certification when it’s about to expire?
At this point, you already understand the basics to maintain your ISO 27001 certification. Now the question becomes, what can you do once it expires?
Fortunately, renewing your certification isn’t that complicated.
In the words of Haider, “Certification bodies keep track of their certification clients accreditation. Auditors will work with you to plan, schedule, and renew ISO 27001 certification.”
In other words, make sure to keep in continuous communication with your current auditor to anticipate your next security audit.
7. What else should our readers know about maintaining ISO 27001?
Haider shares one last word of advice: “Having a compliance technology platform can provide organizations the necessary process structure to implement ISO 27001 certification.”
Other important things to consider include:
- Training your team: Communicate the value of ISO compliance and make sure your team understands the process. This will make it easier to maintain your certification.
- Finding the right certification body: Look for someone with experience in your industry, since it can speed up the audit process and help you get valuable insights to improve your security compliance.
The Verdict
Getting your ISO 27001 certification is an important step for any organization. Keeping that certification over the long term, though, is crucial.
By following the ideas and guidelines provided in this interview, you’ll be able to stay compliant and keep your confidential information secure.
If you’re looking for further guidance on your certification process, Secureframe can help you streamline your ISO 27001 compliance and save you lots of headaches along the way.

Emily Bonnie
Senior Content Marketing Manager
Emily Bonnie is a seasoned digital marketing strategist with over ten years of experience creating content that attracts, engages, and converts for leading SaaS companies. At Secureframe, she helps demystify complex governance, risk, and compliance (GRC) topics, turning technical frameworks and regulations into accessible, actionable guidance. Her work aims to empower organizations of all sizes to strengthen their security posture, streamline compliance, and build lasting trust with customers.

Cavan Leung
Senior Compliance Manager
Cavan Leung, CSSK, CISA, CISSP is an information security leader with over a decade of experience in the security, privacy, and compliance industries. A former auditor and security consultant, Cavan performed ERP and SOX compliance audits at Deloitte, as well as SOC 1, SOC 2, GDPR, and ISO 27001 compliance assessments for Fortune 500 companies at Schellman. At Secureframe, he’s helped hundreds of customers achieve compliance with SOC 2, ISO 27001, GDPR, HIPAA, and more.