
The ISO 27005 Approach to Information Security Risk Management: 2022 Updates Explained
Emily Bonnie
Senior Content Marketing Manager
Cavan Leung
Senior Compliance Manager
ISO/IEC 27005 is one of the most widely recognized standards for information security risk management, especially for organizations building or maintaining an Information Security Management System (ISMS) based on ISO/IEC 27001.
But how does ISO 27005 actually work in practice? Who should use it? What changed with the ISO 27005:2022 update and why does it matter in 2026?
Keep reading to find out the answers and more.
What is ISO/IEC 27005?
In simple terms, ISO/IEC 27005 provides a structured, repeatable risk management process that supports ISO 27001 compliance while remaining flexible enough for organizations of all sizes and industries.
ISO 27005 is part of the ISO 27000 family of standards, created by the International Organization for Standardization (ISO) and the International Electrotechnical Commission (IEC). As part of the ISO 27000 series, this standard helps organizations create, monitor, and continually improve an Information Security Management System (ISMS).
ISO 27005 focuses specifically on information security risk management. Meaning, this international standard provides an organized, systematic approach to identifying, assessing, and managing risks related to information security.
Here's how it relates to other ISO standards:
- ISO 27001: Sets requirements for building, monitoring, and improving an ISMS, including risk management requirements
- ISO 27002: Specifies in detail the information security controls required to implement the ISMS
- ISO 31000: Provides principles and guidelines for managing all types of risks
- ISO 27005: Provides a risk management framework for the ISMS based on ISO 31000 but specifically tailored to information security
ISO 27005 compliance is not a legal or regulatory requirement. But it does lay out the process of completing an information security risk assessment that fulfills the requirements of ISO 27001.

On-Demand Webinar: ISO 27001 for Startups
Need a refresher on ISO 27001? This guide provides an in-depth look at this international standard and what it takes to build and maintain a compliant ISMS.
What is the purpose of ISO/IEC 27005?
The purpose of ISO/IEC 27005 is to provide clear guidance on managing information security risks so that you can better protect your assets and ensure business continuity.
It’s important to understand that the goal of ISO 27007—and information security risk management more broadly—isn’t to completely eliminate all information security risk. That would be neither realistic nor desirable since risk goes hand-in-hand with opportunity. Instead, ISO 27005 is designed to help you:
- Understand what could go wrong
- Evaluate how severe the impact would be
- Decide which risks are acceptable and which must be treated
When done properly, this type of risk management can enable you to understand and define a risk tolerance that’s right for your business and then create a strategy to address risk so you can achieve and maintain the right balance.
ISO 27005 is a well-respected approach to risk management that can be applied across industries, making it a popular choice for organizations searching for a formal risk management methodology. Let's take a closer look at how ISO 27005 compares to other methodologies.
Recommended reading

How to Do an ISO 27001 Risk Assessment
ISO 27005 vs other risk management frameworks
For companies using ISO 27001 to manage an ISMS, ISO 27005 is a clear choice to address the risk management component. But even organizations that aren’t ISO 27001 certified still benefit from using the risk management standard. CISOs, compliance officers, information technology professionals, and other executives rely on ISO 27005 to guide their risk management activities and make informed decisions regarding threats and vulnerabilities.
| Framework | Purpose | Governing Body | Process | Pros Method | Cons |
|---|---|---|---|---|---|
| ISO 27005 | Provides guidelines for creating, implementing, maintaining, and improving information security risk management in support of an Information Security Management System (ISMS) | International Organization for Standardization (ISO) and International Electrotechnical Organization (IEC) | Context establishment, risk identification, risk analysis, risk evaluation, and risk treatment | Flexible, repeatable process; integration with ISO 27001 | No specific ISO 27005 certification |
| NIST 800-53 | Offers a systematic process for understanding vulnerabilities and threats to IT systems | National Institute of Standards and Technology (NIST)a | Threat and vulnerability identification, likelihood and impact determination, risk determination, control analysis | Detailed guidance; integration with NIST RMF | Certain guidelines may be too specific to US federal agencies |
| OCTAVE | Focuses on risk-based information security strategies tailored to an organization's specific business needs and environment | Software Engineering Institute (SEI) at Carnegie Mellon University | Identify goals, key assets, and threats; evaluate vulnerabilities against threats; develop risk mitigation plan and information protection strategy based on identified risks | Takes a holistic view of both organizational and technological risk | May need specific training in OCTAVE method |
Recommended reading

Top 10 Risk Management Methodologies and Frameworks Explained
Benefits of ISO/IEC 27005 for information security risk management
Why do organizations choose ISO 27005 over other risk management methodologies?
- Flexibility: ISO 27005 allows organizations to define their own approach based on their unique business needs and objectives.
- Clear, repeatable process: ISO 27005 lays out five steps for identifying and managing information security risk. It’s a thorough process that ensures organizations fully address their threat landscape, and because it’s a repeatable process, ensures organizations can stay on top of emerging threats as the landscape evolves.
- Support for ISO 27001 compliance: If you’re pursuing or need to maintain ISO 27001 certification, following ISO 27005 ensures you fulfill risk management requirements.
Recommended reading

The ISO 27001 Certification Process: A Step-by-Step Guide
ISO/IEC 27005:2022: The latest updates to the standard
In October 2022, ISO published an updated version of the standard: ISO 27005:2022. This replaced the previous version, ISO 27005:2018.
ISO 27005:2022 introduces several new changes to better align the standard’s terminology and structure with the latest updates to ISO 27001:2022.
Here is a summary of the most significant changes:
- ISO 27005:2022 consolidates the 2018 version’s 12 clauses and six annexes into ten clauses and one annex.
- It establishes a new risk management process with five steps: context establishment, risk identification, risk analysis, risk evaluation, and risk treatment. (The risk acceptance stage has been removed and a new clause introduced: 8.6.3. Acceptance of the residual information security risk. Risk acceptance is now decided after risk treatment.)
- It introduces a new process for identifying information security risks. The 2022 update describes two approaches:
- Event-based approach: Involves identifying risk sources and focusing on the overall threat landscape to define the consequence and severity of each given risk scenario.
- Asset-based approach: Involves identifying asset-specific threats and vulnerabilities, determining their likelihood, and defining specific risk treatment options.
Recommended reading

ISO 27001:2022 and ISO 27002:2022 Explained: How to Comply Before October 2025 Deadline
Getting started: How to manage information security risk with ISO 27005:2022
ISO 27005 lays out five steps for identifying, evaluating, and addressing information security risks.

Step 1: Context establishment
This step is all about establishing the goals and criteria for information security risk management. You’ll need to gather key stakeholders and answer questions like:
- What are your goals for information security and how do they align with your overall business objectives?
- What contractual, regulatory, and compliance requirements need to be taken into account?
- What other risk management approaches exist within the organization, and how will the information security risk management process align with them to ensure consistency?
- How will your organization decide which information security risks to accept and which to mitigate?
Step 2: Risk identification
ISO 27005:2022 lays out two complementary approaches for identifying risk: event-based and asset-based. Organizations can choose to run a single approach independently or use them both together.
- Event-based approach: What are the main events or scenarios that introduce risk? This approach focuses on the organization’s overall threat landscape.
- Asset-based approach: What are the key risks and vulnerabilities associated with each information asset? This approach is more granular and focuses on the organization’s specific assets and architecture.
Step 3: Risk analysis
The risk analysis step is all about narrowing down which systems, services, and data are at risk and how severe each risk or vulnerability is.
While previous versions of ISO 27005 used a qualitative and quantitative risk analysis approach, the 2022 updates add semiquantitative risk analysis.
- Qualitative approach: Consider different scenarios and answer “what if” questions to identify risks.
- Quantitative approach: Use data and numbers to define levels of risk.
- Semi-quantitative approach: Some aspects (such as likelihood) are quantified using statistical methods, and others (such as impact) are defined using subjective methods like expert opinions.
Step 4: Risk evaluation
Once risks have been analyzed, organizations need to decide how to respond to each one. You’ll need to compare each risk against the risk appetite or tolerance criteria you defined in step one. Which risks fall within the acceptable levels, and which need to be treated? This process helps you prioritize risks so you can treat them systematically.
Step 5: Risk treatment
While ISO 27005:2022 does not specify risk treatment options, the previous 2018 standard detailed four possibilities:
- Risk mitigation: Implement information security controls to reduce the likelihood or impact of the risk
- Risk avoidance: Avoid the risk by preventing the circumstances where it could occur
- Risk transfer: Share or transfer the risk to a third party, i.e., by purchasing insurance
- Risk acceptance: Accept the risk because the cost of addressing it outweighs the potential damage
ISO 27005:2022 instead emphasizes the responsibility that risk owners have in creating and approving the risk treatment plan and accepting any residual risks. Risk owners must be involved in deciding which controls will be implemented to treat risks.
In addition, the 2022 update more closely ties ISO/IEC 27005 with ISO/IEC 27001 and ISO/IEC 27002 by introducing the Statement of Applicability. As part of the risk treatment process, all security controls used to modify risk must be compared with those listed in ISO 27001 Annex A.
Recommended reading
What Are ISO 27001 Controls? A Guide to Annex A
Automating the ISO 27005 information security risk management process
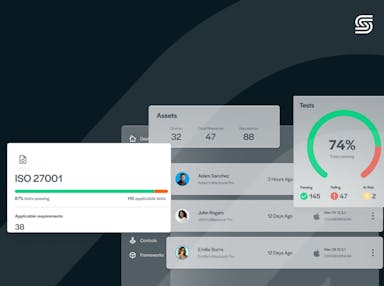
Secureframe’s risk management solution was built on the ISO 27005 standard, simplifying ISO compliance and making it easy to identify both event- and asset-based risk scenarios for your organization.
- AI-powered risk assessment workflow: Comply AI for Risk automates the risk assessment process using artificial intelligence. Get instant insights into each risk based on your organization and company information, including potential impact, likelihood, and recommended treatment.
- Risk library: Select from pre-built risks to quickly identify threats to your organization and assets, including IT, legal, and finance risk categories.
- Risk register + history: Easily document and monitor all your risks in a table view, including risk description, category, assigned owner, risk score, treatment, residual risk score, and status. View risk history to easily show auditors and stakeholders the improvements you’ve made to reduce risk exposure.
- Control linking: Map mitigating security controls to specific risks to seamlessly align your compliance and risk management programs and quickly identify gaps.
See why Secureframe is the leading security and compliance automation platform — schedule a demo with a product expert today.
This post was originally published in November 2023 and has been updated for comprehensiveness.
Use trust to accelerate growth
FAQs
Can you get ISO/IEC 27005 certified?
No, ISO/IEC 27005 is not a certifiable standard. Instead, ISO 27005 is designed to support ISO 27001 certification by explaining how to meet ISO 27001’s risk assessment and risk treatment requirements in a structured, defensible way. Organizations seeking formal certification must undergo an ISO 27001 audit.
Is ISO 27005 required for ISO 27001 certification?
No, but organizations must demonstrate a risk management process during an ISO 27001 certification audit and ISO 27005 is the most commonly accepted approach.
Can small companies use ISO 27005?
Yes. The standard is intentionally flexible and scalable so that organizations of all types and sizes can use it.
Does ISO 27005 replace ISO 27001 risk assessment requirements?
No. ISO 27005 supports and explains how to meet ISO 27001’s risk requirements, it does not replace them.
How often should ISO 27005 risk assessments be performed?
Risk management should be continuous, with formal reviews at least annually or after significant changes.
What is information security risk management?
Information security risk management is the process of understanding what events could transpire to impact your information assets, and what the consequences might be. As with all other types of risk, knowing the threats to your information assets helps you create an effective strategy for protecting them. ISO/IEC 27005 offers a globally recognized methodology for mangaging information security risks to protect your assets and ensure business continuity.

Emily Bonnie
Senior Content Marketing Manager
Emily Bonnie is a seasoned digital marketing strategist with over ten years of experience creating content that attracts, engages, and converts for leading SaaS companies. At Secureframe, she helps demystify complex governance, risk, and compliance (GRC) topics, turning technical frameworks and regulations into accessible, actionable guidance. Her work aims to empower organizations of all sizes to strengthen their security posture, streamline compliance, and build lasting trust with customers.

Cavan Leung
Senior Compliance Manager
Cavan Leung, CSSK, CISA, CISSP is an information security leader with over a decade of experience in the security, privacy, and compliance industries. A former auditor and security consultant, Cavan performed ERP and SOX compliance audits at Deloitte, as well as SOC 1, SOC 2, GDPR, and ISO 27001 compliance assessments for Fortune 500 companies at Schellman. At Secureframe, he’s helped hundreds of customers achieve compliance with SOC 2, ISO 27001, GDPR, HIPAA, and more.