Run Efficient, Structured User Access Reviews in Secureframe
Emily Bonnie
Senior Content Marketing Manager
Fortuna Gyeltsen
Senior Manager, Compliance and Product (Automation)
Most cybersecurity teams are familiar with the annual access review cycle. A reminder hits the calendar, and the process begins: exporting user lists from identity providers and critical systems, consolidating spreadsheets, sending them to system owners for validation, and following up to confirm which permissions should remain or be removed. Once decisions are made, remediation often requires separate tickets and manual tracking to ensure changes are actually completed.
The work gets done, but the process is rarely streamlined. Standardizing it across systems can be difficult, and clearly demonstrating during an audit how decisions were made and whether required changes were implemented is even harder.
At the same time, access risk continues to evolve. Compromised or misused credentials remain one of the most common initial access vectors in data breaches, and over-privileged accounts are a frequent source of audit findings. Employees change roles, contractors transition off projects, and elevated permissions accumulate gradually. Without a structured review process, unnecessary access can persist longer than intended, increasing both cybersecurity exposure and compliance risk.
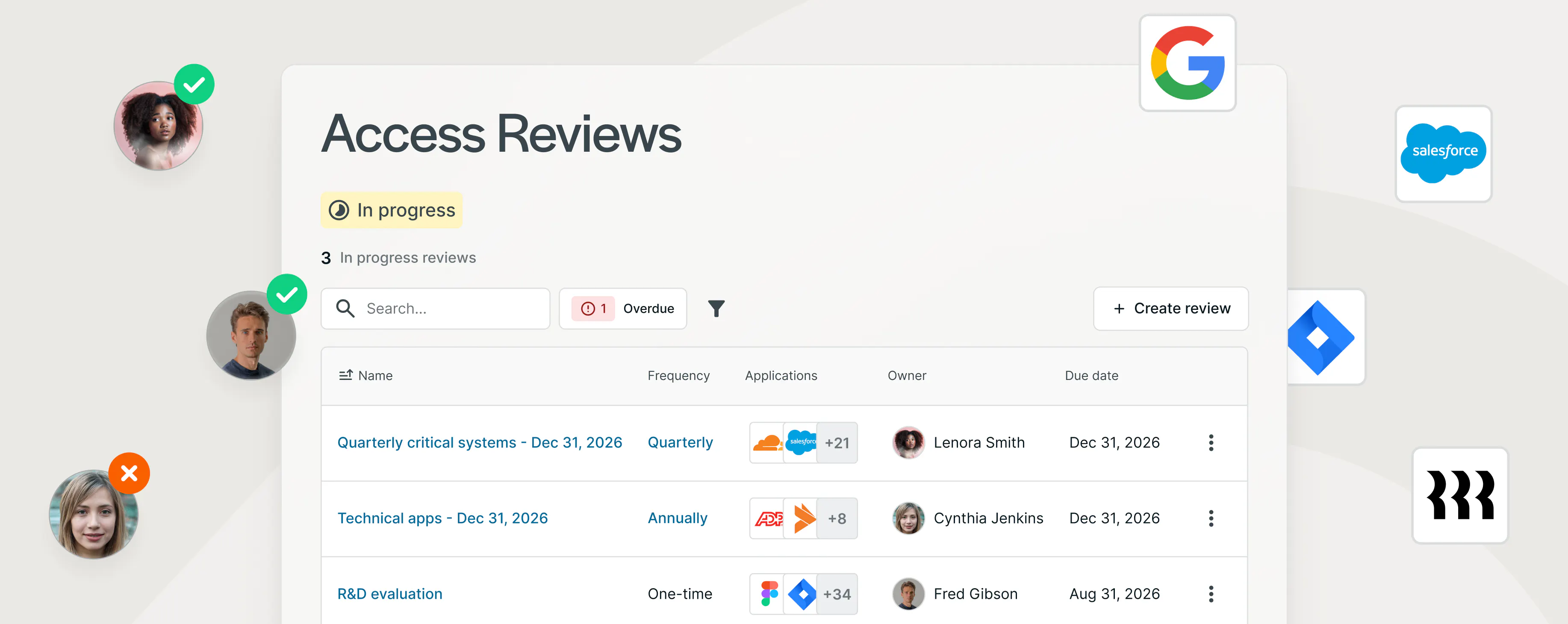
Today, we’re introducing User Access Reviews inside Secureframe. This new workflow centralizes how you assign, complete, and document access reviews across supported systems in Secureframe. You can scope the systems that matter, designate reviewers for each system, evaluate each account against its current role, and track required changes through completion in one place, creating a clear audit trail that aligns with compliance expectations.
User Access Reviews are available as part of the Secureframe Complete package, designed for organizations managing more complex compliance requirements.
Centralize and standardize access reviews across your systems
User Access Reviews turns what is often a manual, follow-up-heavy exercise into a centralized workflow that keeps reviewers accountable and remediation visible from start to finish.
When you set up a review, you start by deciding whether to conduct a one-time or recurring review, then mark which systems should be included. You can pull in applications with direct or custom integrations, systems detected through connected tools such as your identity provider, and manual CSV uploads. Some teams focus only on high-risk applications, while others set periodic review cycles. You can also create a custom scope that reflects how your organization operates.
Before a review begins, each system needs a designated reviewer. Different systems can have different reviewers within the same review, so access decisions stay close to the people who understand the business context. Reviews can run once or repeat on a set cadence, while built-in reminders and clear status indicators reduce the need for manual follow-up and make it easier to keep reviews on schedule.

When a review starts, it runs against a snapshot of access data taken at the review’s start date so that everyone is evaluating access against the same baseline. At the same time, updates made during the review, like assigning account ownership, carry forward to the live record so your access data stays clean and current.
For each account within a system, the reviewer confirms ownership and decides whether access should be maintained, modified, revoked, or marked out of scope. Bulk actions and filters help you move quickly through larger user populations, while still requiring a clear decision for every account.
If access needs to change, reviewers can add notes explaining the decision and create tasks to ensure the change is completed. If you use ticketing tools like Jira or ClickUp, these tasks can sync directly with your existing workflows. Open tasks remain visible within the review until they’re resolved, so required changes don’t get lost.
User Access Reviews also supports non-admin reviewers, allowing system owners and business leaders to participate directly. When a user reviews their own access, they’re prompted to provide a justification, adding an extra layer of oversight where it matters.
Move from periodic manual reviews to ongoing access governance
Access governance only works if reviews actually happen on schedule. Instead of scrambling when a reminder pops up, you can set a defined cadence and let the process run consistently in the background.
When you configure a review, you decide when it starts, how long it stays open, and how often it repeats. Recurring reviews trigger automatically, and upcoming reviews are visible in advance so your team can plan ahead. Clear status indicators show whether a review is upcoming, in progress, nearing its deadline, overdue, or complete.


As new systems are added to Secureframe, you can control how they’re handled in future review cycles. That way, newly onboarded applications don’t quietly fall out of scope. Over time, every completed and in-progress review lives in a centralized table, giving you a clear historical record of how access has been reviewed and managed.
Create a clear, defensible audit trail
Periodic access reviews tend to get a lot of attention during audits. It’s not enough to show that a review happened. Auditors usually want to understand who performed it, what decisions were made, whether access was changed, and how those changes were followed through.
User Access Reviews captures that information as part of the workflow itself. When a review is created, ownership and timelines are defined up front, so it’s clear who was responsible and when the review was completed. As reviewers evaluate each system, their decisions are recorded directly at the account level. If access is modified or revoked, they can document the reasoning and link remediation tasks so there’s a clear record of what was done.
When it’s time to share evidence, executive summaries and exportable reports provide structured documentation without forcing your team to piece together emails, spreadsheets, and ticket screenshots. Instead of reconstructing the story after the fact, the record is already there.

Advancing access governance within Secureframe
Periodic access reviews are often treated as a box to check. In reality, they’re one of the clearest signals of whether access is being actively managed or simply assumed to be correct. When reviews happen consistently and decisions are documented clearly, they reduce unnecessary exposure, limit privilege creep, and demonstrate that access is being evaluated intentionally.
As security programs mature, teams need structured workflows that make it easy to assign responsibility, make clear decisions, and ensure follow-through. Access governance is often where that shift becomes most visible.
User Access Reviews brings that structure into the same platform where monitoring, documentation, and remediation already happen. Instead of managing access governance in parallel tools, it becomes part of your broader security and compliance operations. The result is a process that’s easier to run, easier to explain, and easier to scale.
To see how User Access Reviews works as part of the Secureframe Complete plan, connect with our team for a personalized demo.
Streamline cybersecurity and compliance

Emily Bonnie
Senior Content Marketing Manager
Emily Bonnie is a seasoned digital marketing strategist with over ten years of experience creating content that attracts, engages, and converts for leading SaaS companies. At Secureframe, she helps demystify complex governance, risk, and compliance (GRC) topics, turning technical frameworks and regulations into accessible, actionable guidance. Her work aims to empower organizations of all sizes to strengthen their security posture, streamline compliance, and build lasting trust with customers.
Fortuna Gyeltsen
Senior Manager, Compliance and Product (Automation)
Fortuna Gyeltsen is a former auditor and security consultant with nearly fifteen years of experience in security, privacy, and compliance. As a consultant for Blue Canopy and Coalfire, she developed deep expertise in FISMA, ISO 27001, SOC 2, PCI DSS, BSI C5, and DoD IL 4 and 5. At Secureframe, she worked as a Senior Manager of Compliance and now of Product to help customers automate more of the compliance process so they can focus on big picture improvements rather than shallow work.